Attackers exploited vulnerabilities in Magento environments

A large-scale cyberattack has compromised thousands of Magento-based e-commerce websites, exposing a critical weakness in how online platforms are secured. This is not just another breach. It is a reminder that one vulnerability can impact thousands of businesses at once. What Happened Attackers exploited vulnerabilities in Magento environments to inject malicious code across thousands of […]
Cyber Risks in Healthcare Supply Chains
Cyber threats targeting the healthcare sector continue to evolve, with attackers increasingly focusing on organizations that play a critical role in medical supply chains. A recent security investigation involving Stryker revealed the presence of a malicious file during a probe into a suspected Iran linked cyber incident. While the full scope of the attack is […]
Cyber threats targeting the healthcare sector

Cyber threats targeting the healthcare sector continue to evolve, with attackers increasingly focusing on organizations that play a critical role in medical supply chains. A recent security investigation involving Stryker revealed the presence of a malicious file during a probe into a suspected Iran linked cyber incident. While the full scope of the attack is […]
10,000 users reported issues during the peak of the disruption.

One of the world’s most widely used social media platforms recently experienced a significant disruption, highlighting the fragility of modern digital infrastructure. A widespread outage affected Instagram, leaving thousands of users unable to send direct messages, refresh feeds, or post content across the platform. The disruption was reported globally, with the highest number of complaints […]
15,000 fake domains

A Sophisticated Hybrid Scam Uncovered Cybersecurity researchers recently uncovered a large-scale phishing and malware campaign targeting TikTok Shop users, known as FraudOnTok (previously ClickTok). The operation involves over 15,000 fake domains impersonating TikTok Shop to spread malware and steal cryptocurrency. These malicious websites are promoted using AI-generated influencer videos, fraudulent ads on Meta platforms, and […]
The Evolving Challenge of Phishing as a Service

Cybercriminal ecosystems continue to demonstrate resilience even in the face of law enforcement action. A recent case involving Tycoon 2FA shows how advanced phishing platforms can remain operational despite takedown attempts, raising concerns about the persistence and adaptability of modern cyber threats. This development highlights a critical shift in cybercrime where phishing is no longer […]
Infiltrating over 600 organizations across 80 countries

The China-linked Advanced Persistent Threat (APT) group known as Salt Typhoon has waged an expansive espionage campaign against global networks, infiltrating over 600 organizations across 80 countries, including around 200 in the U.S. Key Impact & Tactics: Targeted Sectors: Telecommunications, government, transportation, lodging, and military infrastructure have all been compromised. Initial Access via Known Vulnerabilities: […]
Modern Fraud Attack Lifecycle
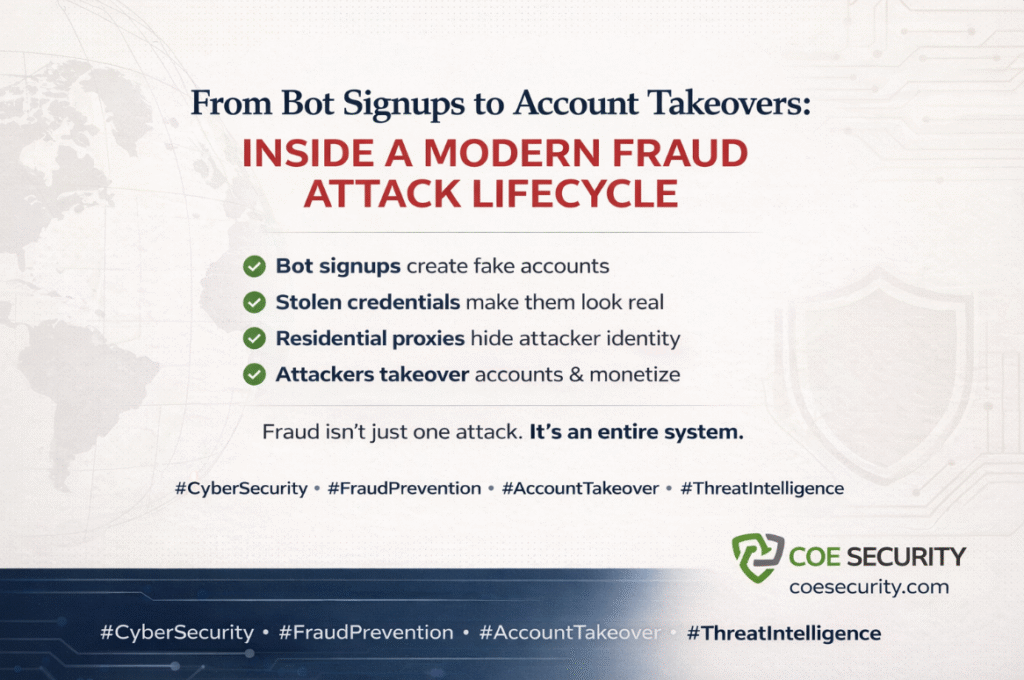
Cyber fraud is no longer a single event. It is a multi-stage, automated operation designed to bypass defenses and exploit digital ecosystems at scale. Recent threat intelligence highlights how attackers are orchestrating fraud campaigns that begin with bot-driven account creation and evolve into full-scale account takeover attacks. Stage 1: Bot-Driven Fake Account Creation Attackers start […]
16 billion user credentials leaked
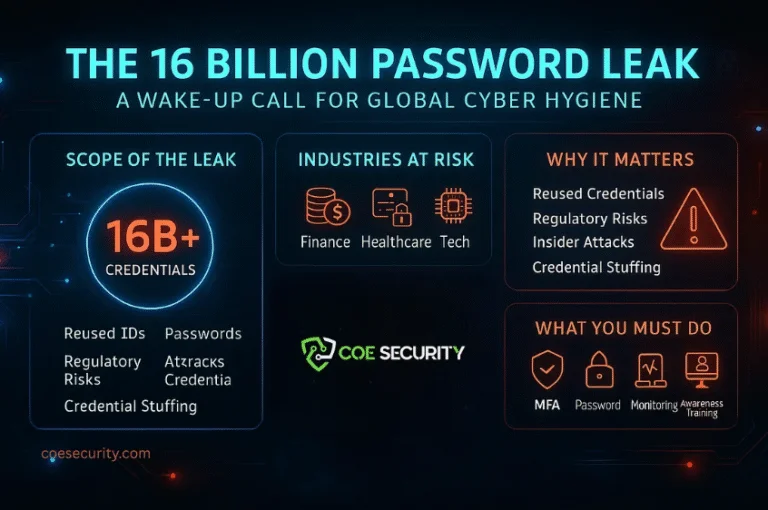
the cybersecurity community witnessed a chilling milestone – over 16 billion user credentials were discovered bundled into a single aggregation, accessible across dark web forums and criminal marketplaces. This data, pulled from previous breaches and information-stealing malware over the years, offers cybercriminals a powerful weapon. Not because it’s new, but because of its volume, accuracy, […]
Exploitation of SolarWinds

Security teams are confirming active exploitation of a critical vulnerability in SolarWinds Web Help Desk, allowing attackers to achieve remote code execution (RCE) on systems that often operate with elevated privileges. This is not just another software flaw. It represents a broader and more dangerous shift in attacker strategy: IT management and help desk platforms […]
