Center of Excellence Security - Application Penetration Testing
Application Penetration
Testing Services
Shield Your Applications – Uncover Vulnerabilities and Protect Web, Mobile, and Cloud Solutions Against Advanced Threats!
Application Penetration Testing at COE Security
At COE Security, our Application Penetration Testing (App Pen Test) service helps organizations identify and address security vulnerabilities in their applications before they can be exploited by malicious actors. As applications become increasingly complex and interconnected, ensuring their security is crucial in protecting sensitive data, maintaining customer trust, and ensuring business continuity. Our App Pen Test service simulates real-world cyberattacks to evaluate the strength of your applications’ defenses and provide actionable insights for improving security.
We perform comprehensive testing across web, mobile, and enterprise applications to identify vulnerabilities in code, architecture, and configuration. Our team of skilled penetration testers uses a combination of automated tools and manual techniques to thoroughly assess the security of your applications and uncover weaknesses that could be exploited in an attack.
With COE Security’s Application Penetration Testing, you can confidently launch and maintain secure applications, ensuring that your digital assets are protected against evolving threats.
Application Penetration Testing at COE Security
Define scope and target applications: Identify platforms, environments, components, and user roles to be included in the assessment.
Map application architecture and flows: Understand data flows, user interactions, and backend integrations to identify attack surfaces.
Enumerate endpoints and input vectors: Discover all accessible pages, APIs, and input points to prepare for comprehensive testing.
Assess authentication and session control: Evaluate login mechanisms, token handling, MFA, and session management for weaknesses.
Test for input validation flaws: Identify injection issues like SQLi, XSS, or command injection using manual and automated methods.
Analyze access controls and privilege checks: Check for broken access controls, IDORs, and horizontal or vertical privilege bypasses.
Evaluate business logic implementation: Test workflows and transactions to uncover abuse scenarios or logical bypass techniques.
Review error handling and security headers: Assess debug messages, response codes, and missing headers that reveal application state.
Conduct client-side and JavaScript analysis: Review exposed logic, API calls, and storage in browser-based or hybrid applications.
Report findings with fix recommendations: Provide a full report with risk ratings, PoCs, and tailored remediation guidance.
Code Assisted
Business Logic Flaws
Indepth Validation
API security
Application Penetration Testing Process
Our established pentest methodology delivers comprehensive testing and actionable recommendations.
Analyze
Threat Model
Active Testing
Business Logic Analysis
Reporting
Why Choose COE Security’s Application Penetration Testing?
-
End-to-end application testing expertise: We assess web, mobile, desktop, and cloud apps with deep contextual understanding.
-
OWASP-aligned and beyond: Our methodology covers OWASP Top 10 and business logic flaws missed by automated scanners.
-
Manual testing with automation support: We blend expert-driven analysis with tools to ensure efficiency and depth of coverage.
-
Platform-aware testing techniques: We tailor tests to the technology stack whether it’s .NET, Java, React, Android, or Swift.
-
Real-world threat simulation: Our tests mimic attacker behavior to uncover risks that affect real users and operations.
Secure development lifecycle support: We integrate with CI/CD tools and provide guidance to improve future security posture.
Clear, developer-friendly reports: Our deliverables include actionable steps, code references, and retesting for verified closure.
Retesting and validation included: Every engagement includes post-remediation testing to ensure issues are fully resolved.
PTaaS dashboard for visibility: Clients receive real-time updates, collaboration tools, and access to findings via our secure portal.
Trusted by startups and enterprises alike: We serve regulated industries, SaaS providers, and fintechs with proven outcomes.
Five areas of Application Penetration Testing
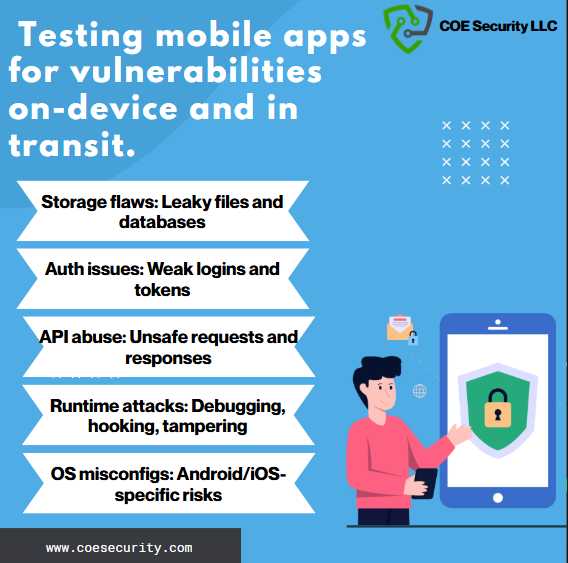
Mobile Application
Mobile Application Penetration Testing service is tailored to secure your iOS and Android applications against evolving threats. We analyze vulnerabilities such as insecure data storage, weak encryption, improper session management, and API misconfigurations. Our testing process combines dynamic analysis, reverse engineering, and real-world attack simulation to uncover security gaps. To assist your development team, we provide detailed remediation steps, including code snippets and secure coding best practices, ensuring vulnerabilities are resolved effectively. With our expertise, you can deliver safe, high-performing mobile applications that protect user data and maintain trust.

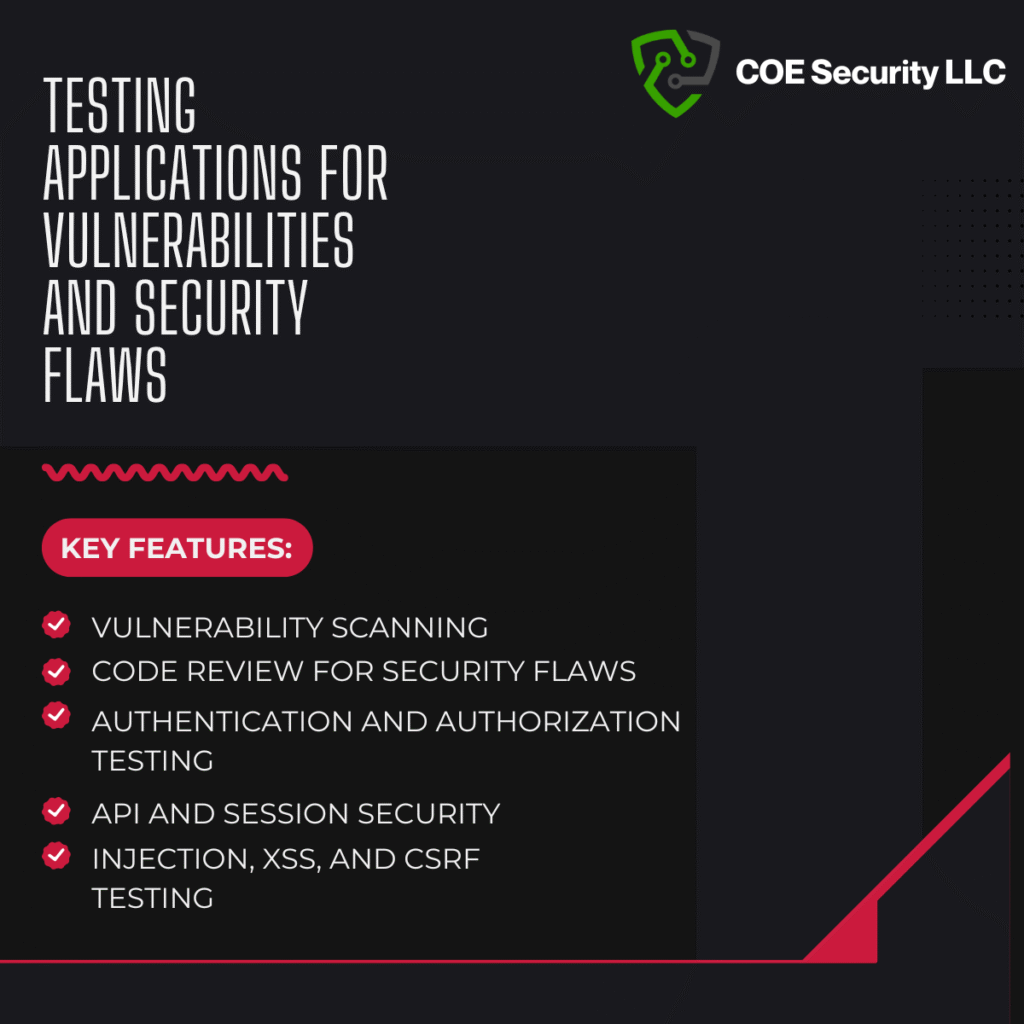
Web Application
Web applications are a prime target for attackers, making their security a critical priority. Our Web Application Penetration Testing service identifies vulnerabilities such as SQL injection, cross-site scripting (XSS), broken authentication, and misconfigured security headers. Using a combination of automated tools and manual testing, we thoroughly assess your application based on OWASP Top 10 guidelines and beyond. Post-assessment, we provide actionable insights, detailed remediation guidance, and secure code snippets to address identified issues. Our goal is to help you fortify your web applications against potential exploits while enabling a secure user experience.

Thick Client
Thick client applications, often used in enterprise environments, pose unique security challenges. Our Thick Client Penetration Testing service evaluates vulnerabilities in both the client-side application and its interaction with backend servers. We focus on issues such as insecure local data storage, improper authentication, reverse engineering risks, and network-level attacks. Our experts identify weaknesses and provide developers with clear remediation steps, including code examples to mitigate risks efficiently. This ensures that your thick client applications remain secure, stable, and compliant with industry standards.
API Security
APIs are the backbone of modern applications, facilitating data exchange and integration, but they also introduce potential vulnerabilities. Our API Security Testing service assesses your APIs for flaws such as broken authentication, excessive data exposure, and improper access controls, following OWASP API Security Top 10 guidelines. We conduct rigorous endpoint testing to identify risks and provide detailed recommendations for securing your APIs. Along with prioritized findings, we offer tailored code snippets and best practices to help your team address vulnerabilities effectively. With our expertise, your APIs will be robust, scalable, and resistant to malicious exploitation.
Firmware Security
Firmware forms the foundation of hardware functionality and is increasingly targeted by attackers. Our Firmware Security Testing service focuses on identifying vulnerabilities such as insecure boot processes, hardcoded credentials, and unprotected firmware updates. We analyze firmware binaries, configuration files, and underlying code to detect and address risks. To support your engineering team, we provide actionable remediation insights and secure coding recommendations, ensuring your firmware is resilient against both known and emerging threats. With our assistance, you can safeguard your devices and maintain trust in your hardware solutions.
Advanced Offensive Security Solutions
COE Security empowers your organization with on-demand expertise to uncover vulnerabilities, remediate risks, and strengthen your security posture. Our scalable approach enhances agility, enabling you to address current challenges and adapt to future demands without expanding your workforce.
Why Partner With COE Security?
Your trusted ally in uncovering risks, strengthening defenses, and driving innovation securely.”
Expert Team
Certified cybersecurity professionals you can trust.
Standards-Based Approach
Testing aligned with OWASP, SANS, and NIST.
Actionable Insights
Clear reports with practical remediation steps.
Our Products Expertise













Information Security Blog
Data Breach at IMA Diligence Services Highlights the Growing Importance of Third-Party Risk Management
The cybersecurity landscape continues to demonstrate that no organization is immune to…
The Growing Importance of AI Observability: Coralogix’s $200 Million Investment Signals Market Momentum
As organizations accelerate the adoption of Artificial Intelligence across business operations, cybersecurity…
When One Line of Code Becomes a Global Risk: Lessons From a Microsoft Android App Security Exposure
In software development, even the smallest coding oversight can have far-reaching consequences.…