The Supply Chain Attack Risk: When Trust Becomes Your Weakest Link

Your organization may be secure. But are your partners? Modern businesses rely on a complex network of vendors, suppliers, and service providers. These third parties help drive efficiency, scalability, and innovation. But they also introduce risk. Because every external connection expands your attack surface. Attackers understand this. Instead of targeting well-defended organizations directly, they often […]
The Ransomware Evolution: Why It’s No Longer Just About Encryption
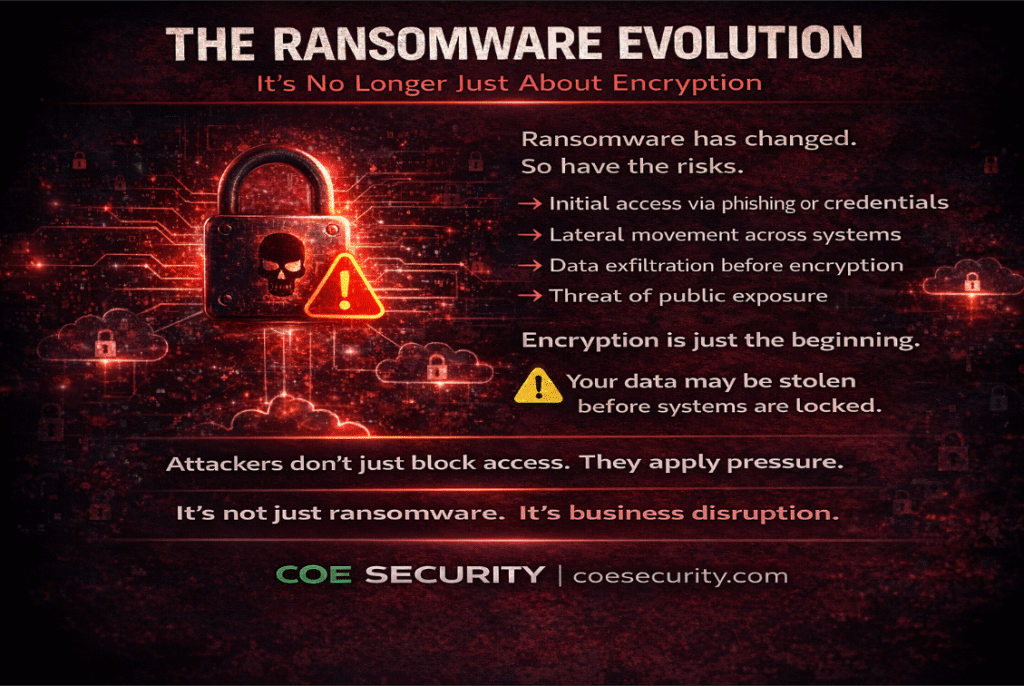
Ransomware has changed. It’s no longer just about locking your files. It’s about controlling your business. In the past, ransomware attacks were straightforward. Attackers encrypted data and demanded payment for its release. Today, the strategy is far more advanced. Modern ransomware attacks are multi-stage operations designed to maximize impact and pressure organizations into paying. Encryption […]
The Insider Threat Risk: When Access Becomes the Attack Vector
Not every threat comes from outside. Some already have access. Organizations invest heavily in firewalls, detection systems, and external defenses. But one of the most underestimated risks comes from within. The insider threat. This does not always mean malicious employees. In many cases, it involves: • Negligent users • Compromised accounts • Third-party access misuse […]
The API Security Risk: The Hidden Door Into Your Systems
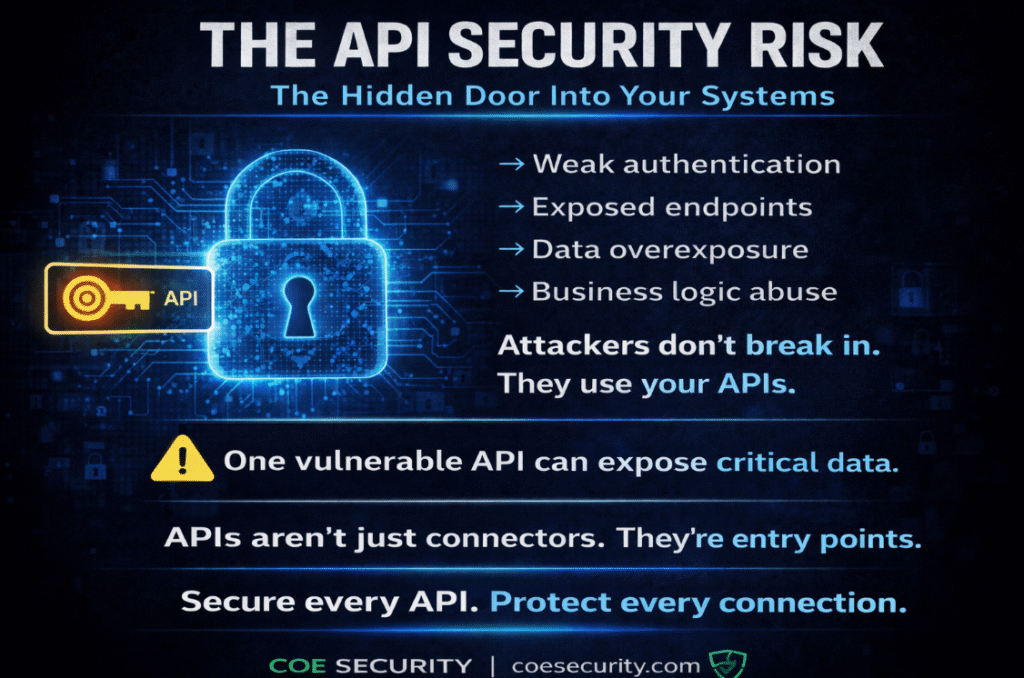
APIs run modern businesses. From mobile apps to cloud platforms, APIs connect systems, enable integrations, and power digital experiences. They are essential for speed, scalability, and innovation. But they also introduce a critical risk. APIs are one of the most exposed parts of your environment. Unlike traditional systems, APIs are designed to be accessed. They […]
The Shadow IT Risk: What You Don’t See Can Hurt You

Not every system in your organization is approved. But many are still in use. Employees today adopt tools faster than security teams can track. From file-sharing platforms to AI tools and SaaS applications, new technologies are introduced into workflows without formal approval. This is known as Shadow IT. And it is growing rapidly. While these […]
The AI Security Gap: Why Protecting AI Systems Is Now a Business Priority
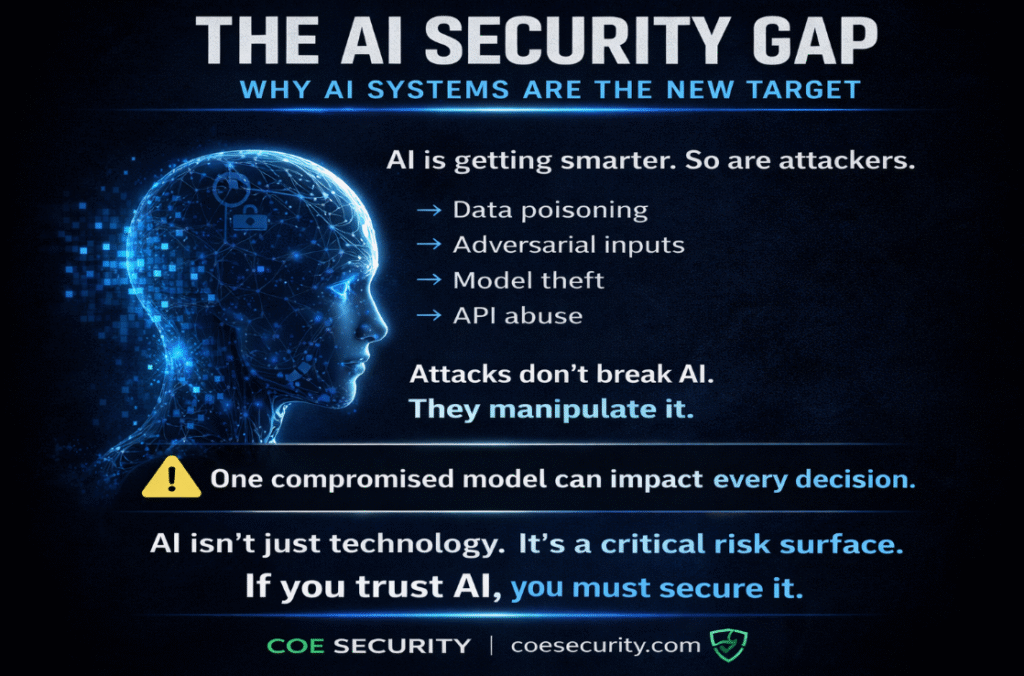
AI is transforming business. From automation to decision-making, organizations are rapidly integrating AI into core operations. It improves efficiency, enhances customer experience, and drives innovation. But it also introduces a new and often overlooked risk. AI systems themselves are becoming targets. Unlike traditional applications, AI models are not just software. They learn from data, adapt […]
The Overlooked Threat: Why Endpoint Security Still Matters More Than Ever
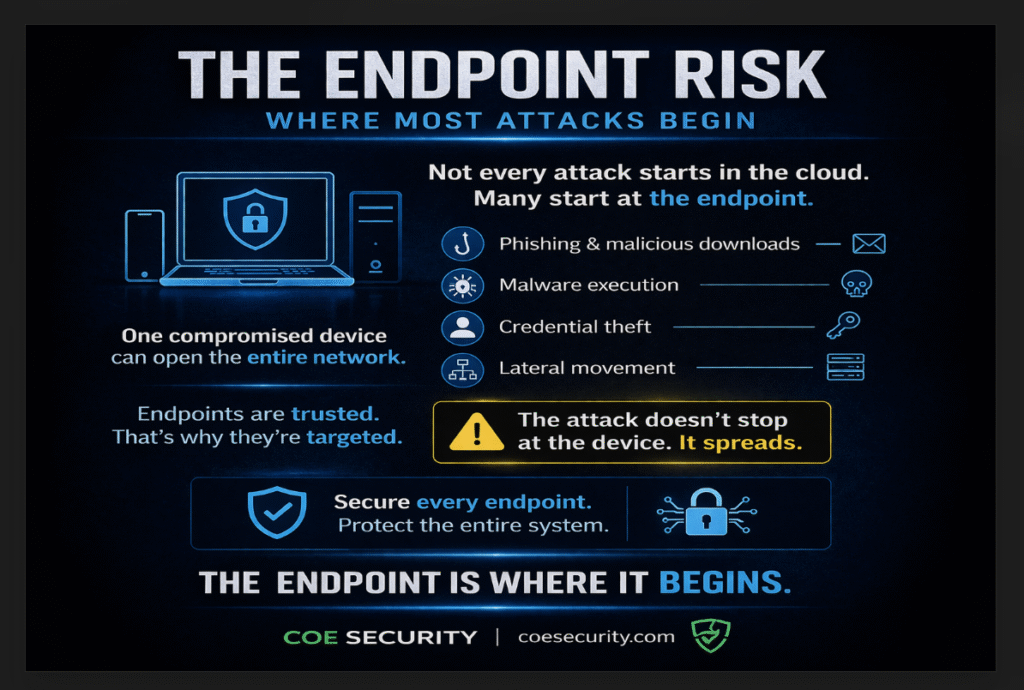
Not every attack starts in the cloud. Many begin at the endpoint. Laptops, desktops, mobile devices, and remote systems are the front line of modern organizations. They are where users interact, data is accessed, and credentials are entered. And that makes them a prime target. As workforces become more distributed, endpoints have expanded beyond traditional […]
The Patch Delay Problem: Why Unpatched Systems Are Easy Targets
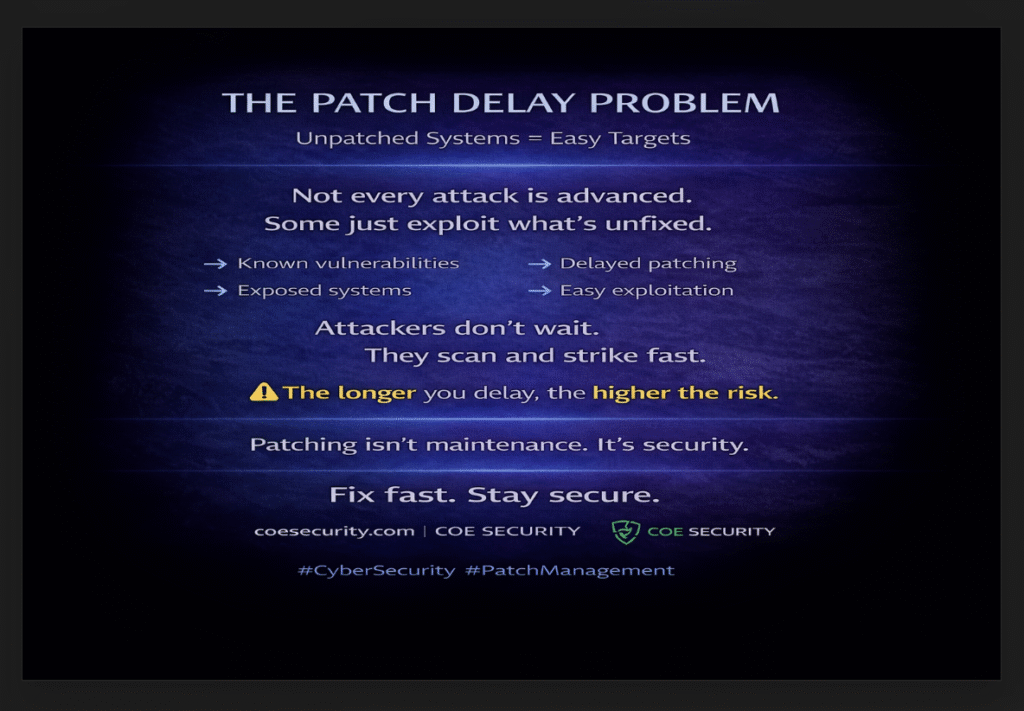
Not every attack is sophisticated. Some just exploit what was never fixed. Organizations invest heavily in security tools, monitoring systems, and defenses. But one of the most common causes of breaches is far simpler. Delayed patching. Software vulnerabilities are discovered every day. Vendors release patches to fix them. But when those patches are not applied […]
The Alert Fatigue Problem: When Too Many Alerts Become a Security Risk
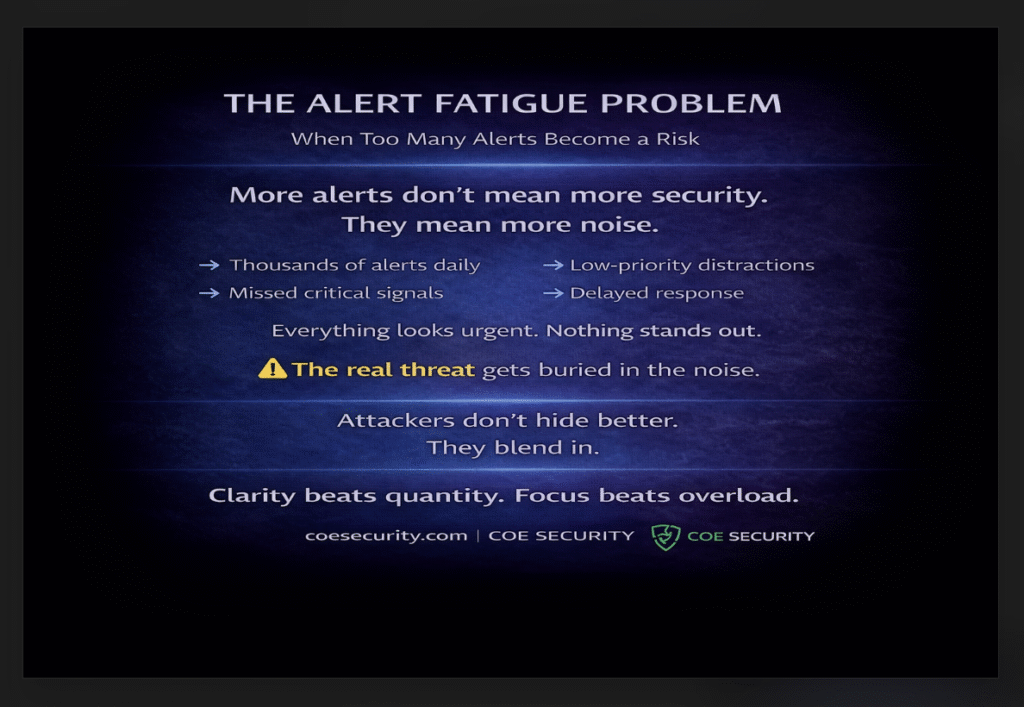
More alerts do not mean more security. In fact, they can mean the opposite. Security teams today are overwhelmed. Monitoring tools generate thousands of alerts daily, each signaling a potential issue. While these alerts are meant to improve visibility, they often create noise instead of clarity. This leads to a dangerous problem. Alert fatigue. When […]
The Third-Party Risk: When Your Security Depends on Someone Else

Your security is only as strong as your weakest vendor. Modern organizations rely heavily on third-party providers. Cloud services, SaaS platforms, vendors, and partners are deeply integrated into daily operations. They bring speed, scalability, and efficiency. But they also introduce risk. Every external integration expands your attack surface. And often, these external systems have access […]
