ACCESS IS THE REAL ATTACK SURFACE

Not all users should see all data Data exposure isn’t just about where data exists. It’s about who can access it. Most organizations focus heavily on securing infrastructure – firewalls, endpoints, networks. But breaches often bypass all of that. They happen through legitimate access. An employee with excessive permissions. A third-party vendor with outdated access […]
API Security: The Weakest Link in Modern Digital Ecosystems
APIs are the backbone of modern applications. They connect services, enable integrations, and power everything from mobile apps to enterprise platforms. But as organizations expand their digital footprint, APIs have quietly become one of the most targeted and vulnerable entry points for attackers. In many cases, the application itself is secure. The API behind it […]
Shadow IT: The Silent Security Gap Most Organizations Ignore
Every organization invests in cybersecurity tools, policies, and compliance frameworks. Yet, one of the most significant risks often grows unnoticed within the environment itself. Shadow IT. It refers to applications, devices, and services used by employees without approval or visibility from the IT or security team. While often adopted for convenience or productivity, Shadow IT […]
The Hidden Risk Inside Modern Enterprises: Why Identity Security Is Becoming the New Cyber Battlefield
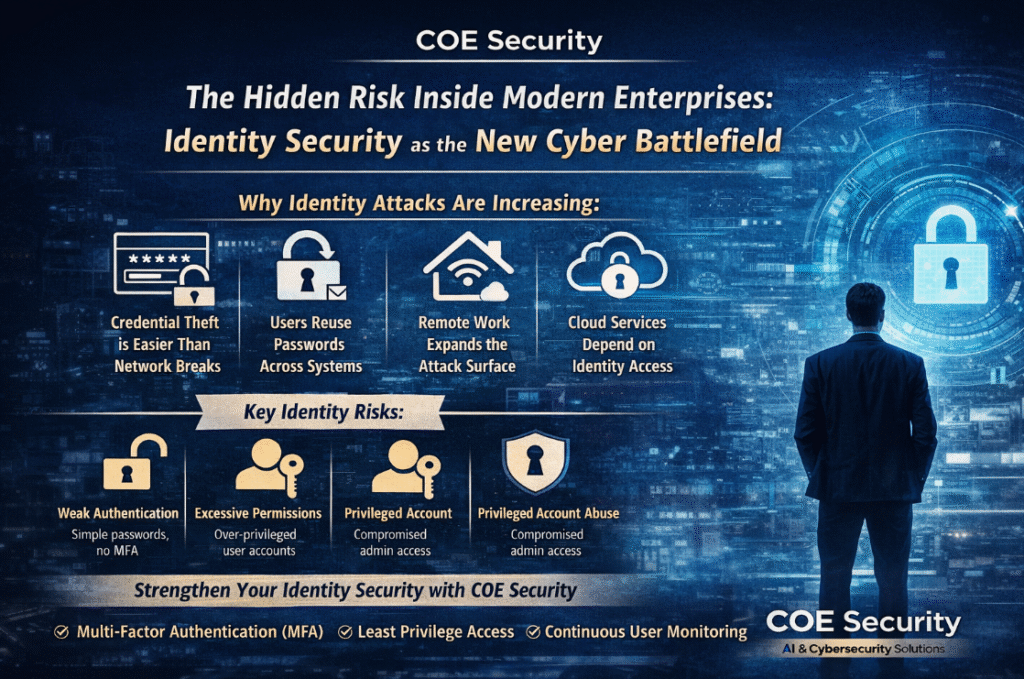
As organizations move deeper into cloud adoption, remote work, and AI-driven systems, one security area has quietly become the primary target for attackers: identity. Today, identity is no longer just a login mechanism. It is the new perimeter of enterprise security. Whoever controls identity access often controls the entire system. Why Identity Has Become the […]
The Data Exposure Risk: Why Sensitive Data Is Still Your Biggest Liability
Data is your most valuable asset. But it’s also your biggest risk. Organizations collect, process, and store massive amounts of sensitive data — customer information, financial records, health data, intellectual property. This data drives business. But it also attracts attackers. Because where there is data, there is value. Data exposure doesn’t always happen through complex […]
The API Security Risk: The Silent Gateway Attackers Exploit
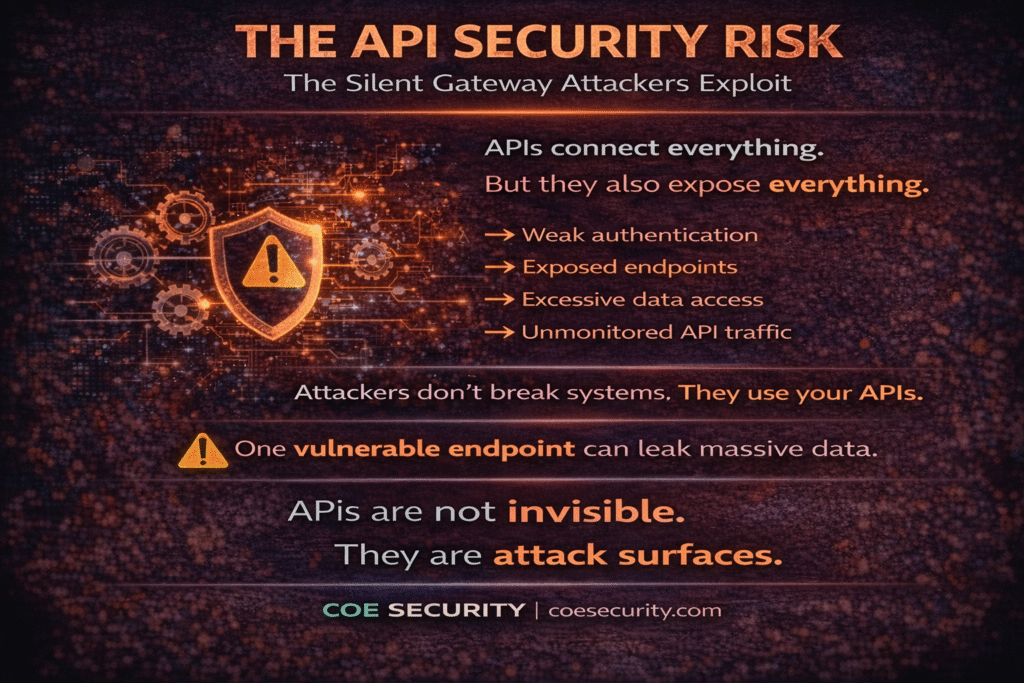
APIs power everything. From mobile apps and cloud services to third-party integrations and internal systems, APIs are the backbone of modern digital infrastructure. But they are also one of the most overlooked security risks. Because APIs are designed to be accessible. They expose data, enable communication, and connect systems. That’s their purpose. And that’s exactly […]
The Shadow IT Risk: What Your Organization Can’t See Can Hurt You
Not all systems are approved. But they are still in use. Shadow IT refers to applications, tools, and services used within an organization without the knowledge or approval of the IT or security team. And it’s everywhere. Employees adopt tools to move faster, collaborate better, and solve problems quickly. From cloud storage and messaging apps […]
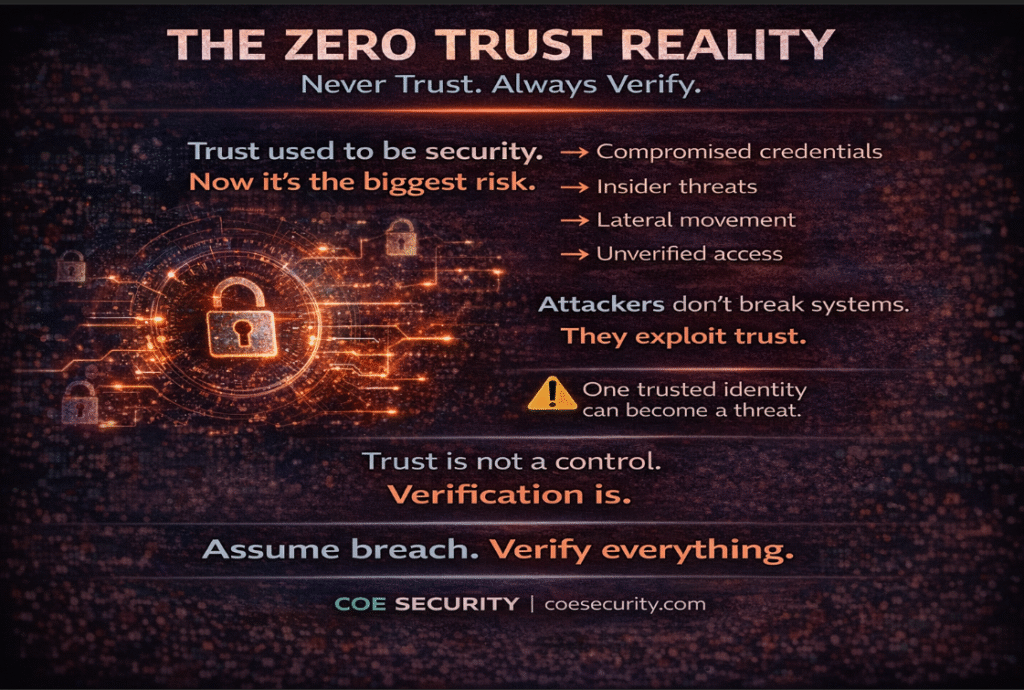
The Zero Trust Reality: Why “Never Trust, Always Verify” Is No Longer Optional

Trust used to be the foundation of security. Once inside the network, users and systems were often trusted by default. Access was granted, and little verification followed. That model no longer works. Modern environments are complex, distributed, and constantly changing. Cloud adoption, remote work, third-party integrations, and mobile access have dissolved traditional network boundaries. There […]
The Endpoint Security Risk: Why Every Device Is a Potential Entry Point
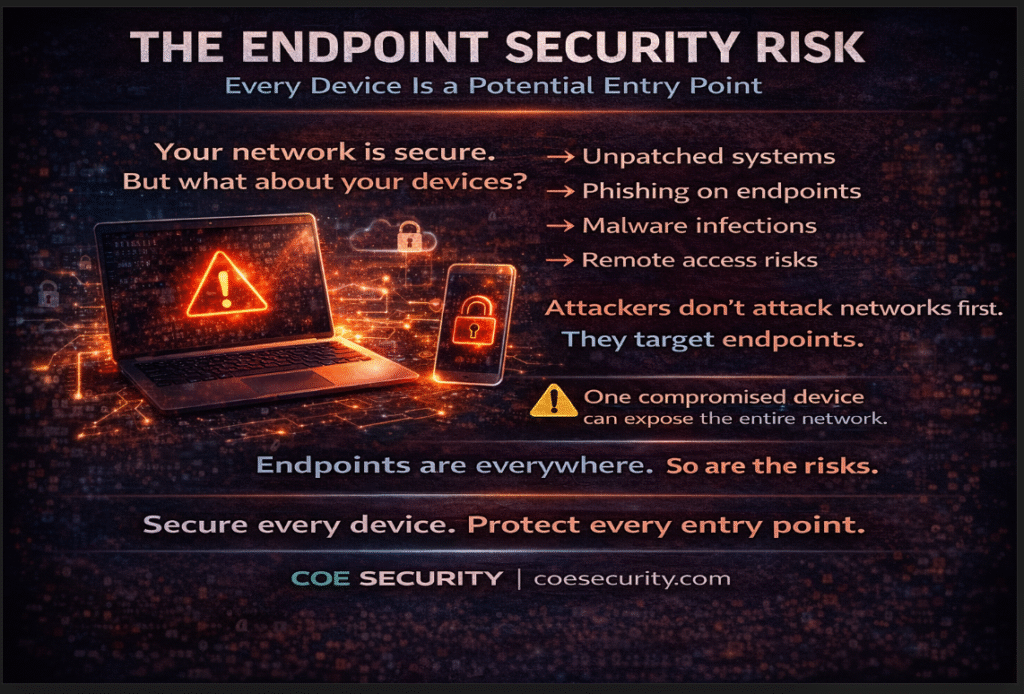
Your network is only as secure as its endpoints. Laptops, mobile devices, servers, and IoT systems are all critical parts of modern infrastructure. They enable productivity, connectivity, and scalability. But they also expand your attack surface. Every endpoint is a potential entry point. Attackers increasingly target endpoints because they are numerous, distributed, and often inconsistently […]
The Password Problem: Why Credentials Are Still the Easiest Way In
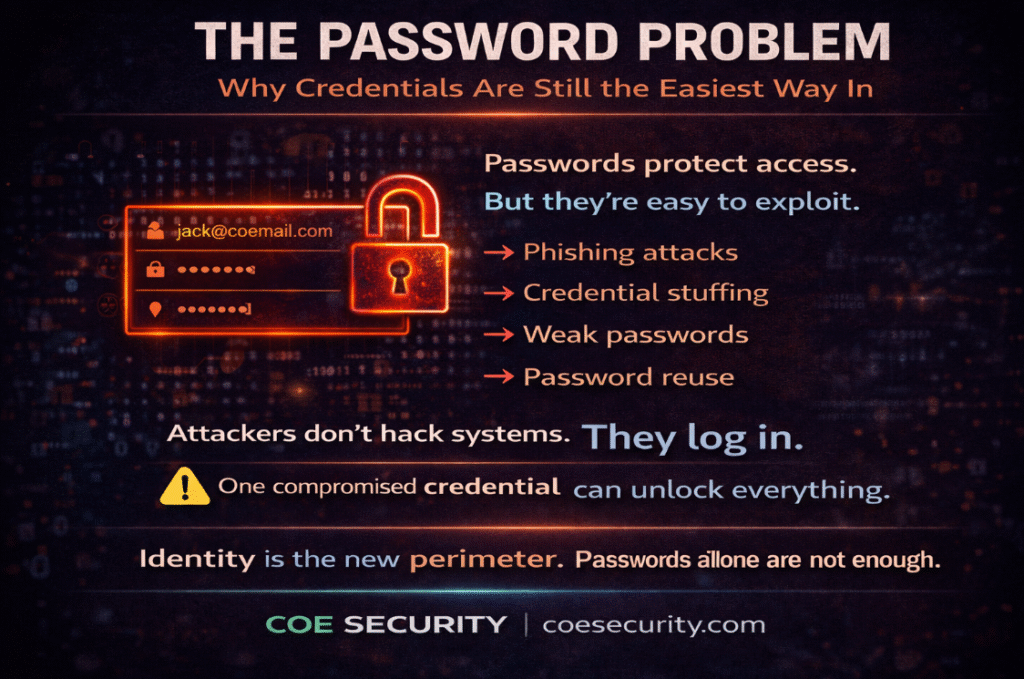
Despite all advancements in cybersecurity, one issue remains unchanged. Passwords are still the weakest link. Organizations invest in advanced security tools, AI-driven detection, and complex architectures. Yet attackers often don’t need sophisticated techniques. They just log in. Credential-based attacks continue to dominate because they are simple, scalable, and effective. With access to stolen or weak […]
