Containment Is Not the End of the Incident
On December 15, 2025, SoundCloud confirmed unauthorized access to user data affecting approximately 20% of its global user base. The attackers exfiltrated email addresses and public profile information. Importantly, no passwords, authentication secrets, or financial data were compromised. From a narrow technical perspective, this distinction matters. It prevented immediate account takeover, direct financial fraud, and […]
SYSTEM-Level Code Execution
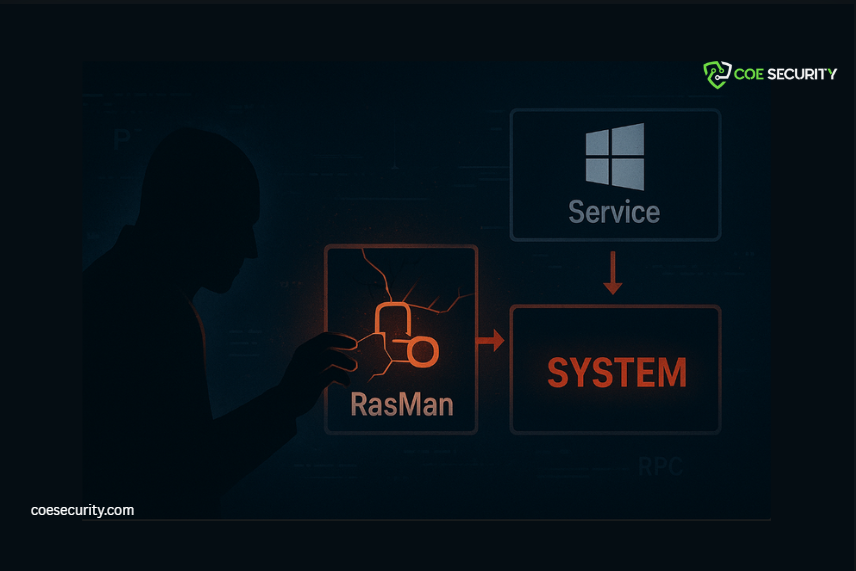
A critical weakness has been identified in Windows Remote Access Connection Manager (RasMan) that enables local attackers to achieve SYSTEM-level code execution. What makes this issue especially dangerous is not a single vulnerability-but a chained exploitation technique that breaks long-standing Windows security assumptions. Executive Summary Impact: Full local privilege escalation to NT AUTHORITY\SYSTEM Attack Type: […]
React RSC Flaw

Active exploitation of CVE-2025-55182 is now enabling attackers to gain full remote code execution on React Server Component–based applications. More than 644,000 domains and 165,000 IPs are currently exposed. The vulnerability impacts Next.js, Waku, Vite RSC implementations, and custom React servers, making it a cross-framework, internet-scale threat. What Is Actually Going Wrong The flaw stems […]
GOLD BLADE’s QWCrypt Locker Threat
What began as a pure espionage operation has now evolved into something far more destructive. GOLD BLADE-also tracked as RedCurl, RedWolf, and Earth Kapre-has shifted from silent data theft to a hybrid model that combines intelligence gathering, data exfiltration, and targeted ransomware deployment using a custom locker known as QWCrypt. Between February 2024 and August […]
The Hidden Weakness in AI Coding

AI-driven IDEs are rapidly becoming embedded in modern development workflows. They accelerate coding, automate repetitive tasks, and provide real-time debugging support. But new research shows they also introduce a class of security risks we are not prepared for. More than thirty vulnerabilities have already been uncovered across major AI coding tools. Several of these flaws […]
The Expanding Attack Surface
This week’s cybersecurity developments reveal a sobering reality: attackers are now exploiting both legacy vulnerabilities and modern AI-enabled platforms with equal precision. From the rapid weaponization of the React2Shell flaw to the resurgence of USB-based malware and the emergence of critical vulnerabilities within AI-powered development tools, the threat landscape is widening at a rate that […]
AI-Powered Cyber Intrusions

The cybersecurity world is entering a new and unsettling era where attackers no longer need phishing emails, malicious links, or social engineering tactics to infiltrate systems. A growing and deeply concerning threat vector has emerged – Zero Click Agentic Browser Attacks. These attacks reflect a fundamental shift in how cyber adversaries operate in an age […]
AI Models Are Becoming Attack Targets.

Artificial intelligence is no longer just a business enabler. It is now one of the most aggressively targeted layers in the modern attack surface. Recent security research reveals a sharp rise in attempts to manipulate, extract, poison, or exploit generative AI models used across critical industries. The finding is clear. As organizations adopt AI for […]
Malicious Visual Studio Code (VS Code) extensions

In 2025, researchers discovered a new wave of malicious Visual Studio Code (VS Code) extensions that threaten developers, software teams, and entire organizations. What appears as a helpful plugin can become a vehicle for cryptomining, credential theft, remote backdoors, or supply-chain compromise. This highlights a growing trend: developer tools themselves are being weaponized, and the […]
Coupang’s 33.7 Million‑User Breach

On 29 November 2025, Coupang, South Korea’s largest e-commerce platform, confirmed a massive data breach affecting approximately 33.7 million customer accounts. Personal information including names, email addresses, phone numbers, delivery addresses, and order histories were exposed. While payment credentials and login passwords were reportedly safe, the incident poses a long-term risk for identity theft, phishing […]
