Shai-Hulud Worm Source Code Released: A New Wake-Up Call for Cyber Defenders
The public release of malware source code often marks the beginning of…
Protect your IoT and embedded systems with expert insights and tailored remediation strategies. Stay ahead of emerging threats and ensure the integrity of your technology and operations.
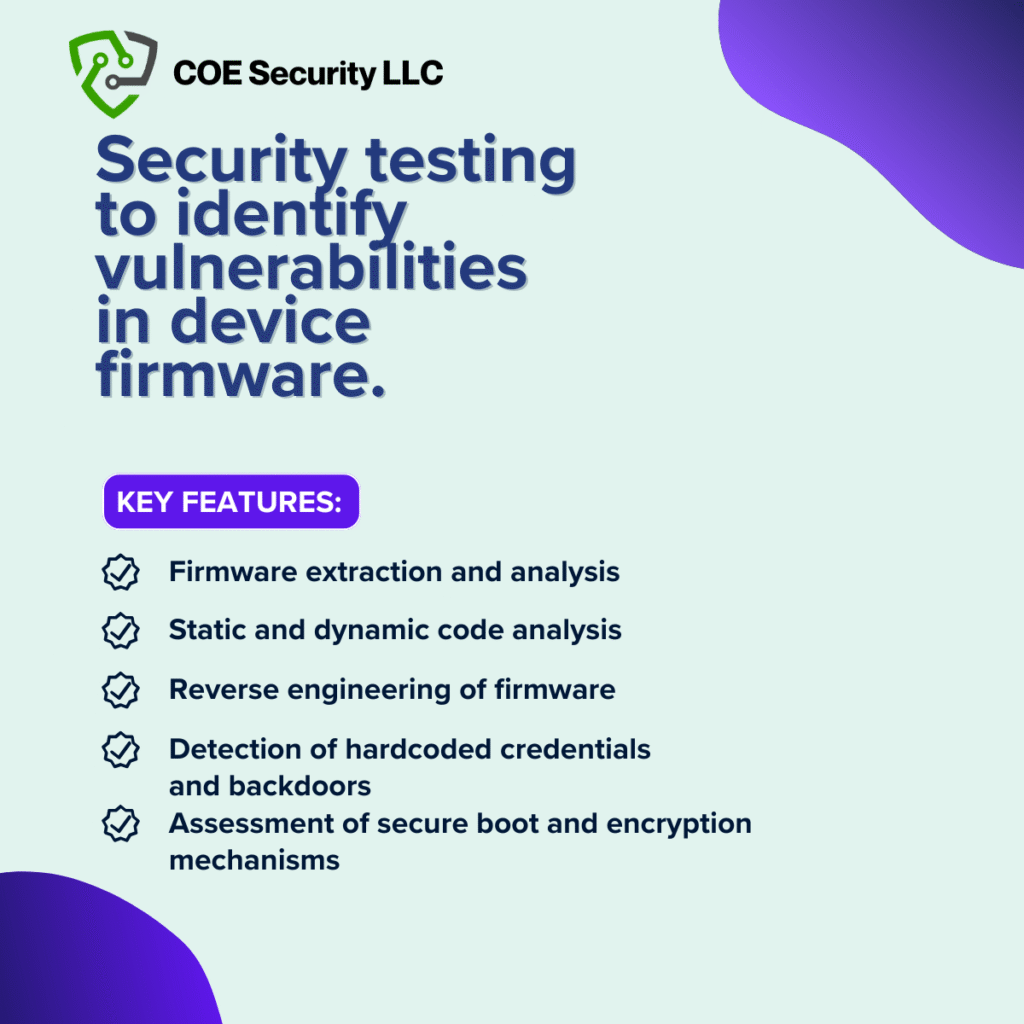
At COE Security, our Firmware Penetration Testing service is designed to evaluate the security of embedded systems and devices by identifying vulnerabilities within their firmware. Firmware is an integral part of hardware, controlling how devices operate, and its security is crucial for safeguarding against cyberattacks. Vulnerabilities in firmware can lead to persistent, hard-to-detect threats that can compromise the functionality, security, and integrity of the device and the network it connects to.
Our experts conduct in-depth testing to uncover flaws in the firmware that could be exploited by attackers, such as hardcoded passwords, insecure communication protocols, or vulnerabilities in bootloaders and update mechanisms. By assessing the firmware at various stages such as pre-deployment, in-use, and during updates we ensure that your embedded systems are resilient against attacks that target their underlying software.
With COE Security’s Firmware Penetration Testing, you can identify hidden security risks in your devices and take proactive steps to safeguard them from exploitation, ensuring that your hardware meets the highest security standards.
Define scope and target devices: Identify the firmware versions, hardware models, and system components to be included in testing.
Extract firmware from devices: Use techniques like UART, JTAG, SPI, or vendor updates to obtain the firmware binary for analysis.
Perform static firmware analysis: Decompress and dissect firmware images to explore file systems, configurations, and code.
Reverse engineer binaries and logic: Analyze executables, scripts, and compiled code to discover logic flaws or hidden backdoors.
Search for hardcoded secrets: Identify embedded credentials, API keys, tokens, and private certificates left inside the firmware.
Assess update mechanisms and OTA: Evaluate firmware signing, encryption, and version control to test for secure update delivery.
Emulate or simulate firmware: Run the firmware in controlled environments to observe runtime behavior and simulate attacks safely.
Test for system-level vulnerabilities: Check for outdated libraries, weak permissions, privilege escalation, and exposed services.
Validate cryptographic implementations: Review encryption, hashing, and key storage practices for weak or broken cryptographic use.
Document findings with fix guidance: Deliver technical reports with PoCs, risk levels, and secure coding recommendations.
Our established methodology delivers comprehensive testing and actionable recommendations.
Deep expertise in firmware analysis: Our team specializes in embedded systems, reverse engineering, and low-level binary analysis.
Hardware-assisted extraction capabilities: We use industry tools to retrieve firmware even from locked or custom bootloaders.
Custom emulation and sandbox testing: We replicate runtime behavior using QEMU or proprietary tools to observe attack vectors.
Support for secure firmware updates: We assess OTA pipelines, signature validation, and rollback protection for hardened delivery.
Cryptographic hygiene evaluation: We uncover weak cipher use, reused keys, and improper key storage affecting product trust.
Aligned with industry standards: Testing methodology follows NIST, OWASP Firmware Security, and vendor-specific hardening guides.
Transparent, actionable reporting: We deliver clear guidance that engineers can immediately use to strengthen firmware security.
Trusted by device makers and OEMs: COE Security has secured firmware in routers, cameras, IoT devices, and critical hardware.
In Application Security Consulting, we conduct thorough assessments of your product’s authentication and session management mechanisms. This includes testing for vulnerabilities such as weak passwords, session fixation, and session hijacking. Our goal is to ensure that only authorized users can access sensitive parts of your product, and sessions are properly secured. We also evaluate your product’s ability to detect and mitigate unauthorized access attempts in real-time. By addressing authentication flaws and improving session management, we help strengthen your product’s security, safeguarding user data and reducing the risk of unauthorized breaches or privilege escalation.
Software Compliance Testing ensures that your product adheres to relevant security standards and industry regulations. We evaluate how the product handles user inputs, looking for vulnerabilities such as SQL injection, cross-site scripting (XSS), and other common injection flaws. Our team also checks compliance with secure coding practices and data protection laws, such as GDPR or CCPA. We identify potential weaknesses that attackers could exploit and ensure that your product is resilient to security breaches. This service is essential for protecting your system from attacks that target improper input validation and for ensuring regulatory compliance, preventing costly legal issues.
In Cloud Security Consulting, we assess the security of your product’s cloud-based components, including APIs, cloud storage, and communication protocols. We focus on securing cloud infrastructure by testing for insecure APIs, lack of proper authentication mechanisms, and unencrypted data transmissions. By performing these tests, we identify vulnerabilities that could be exploited by attackers, potentially leading to unauthorized access or data breaches. We also evaluate the effectiveness of your cloud security controls, ensuring that they meet industry standards. Our comprehensive approach ensures that your cloud-based product is both secure and compliant with the latest cloud security frameworks.

Compliance as a Service focuses on ensuring that your product meets required regulatory standards for data protection and privacy. Our service includes testing for proper encryption of sensitive data, secure storage practices, and the implementation of secure access controls. We verify that your product complies with relevant regulations such as GDPR, HIPAA, and CCPA to ensure that user data is handled with the highest level of security. Additionally, we test the product’s ability to safeguard data throughout its lifecycle—from input to storage to transmission—helping you avoid costly penalties for non-compliance and building trust with your customers.

Cyber Resilience focuses on evaluating your product’s ability to withstand, recover from, and adapt to security breaches or cyberattacks. We conduct business logic and workflow testing to identify flaws in your product’s functionality that could be exploited by attackers. This includes testing for improper validation of business processes, unauthorized privilege escalation, and critical workflow failures. Our goal is to ensure that even if an attack succeeds, your product can maintain operational continuity, detect issues early, and recover swiftly. We help you implement strategies to minimize downtime and improve your organization’s ability to respond to future security incidents.
COE Security empowers your organization with on-demand expertise to uncover vulnerabilities, remediate risks, and strengthen your security posture. Our scalable approach enhances agility, enabling you to address current challenges and adapt to future demands without expanding your workforce.
Your trusted ally in uncovering risks, strengthening defenses, and driving innovation securely.
Certified cybersecurity professionals you can trust.
Testing aligned with OWASP, SANS, and NIST.
Clear reports with practical remediation steps.






The public release of malware source code often marks the beginning of…
Microsoft has released new technical insights into Kazuar, a sophisticated malware framework…
The speed at which cybercriminals weaponize newly disclosed vulnerabilities continues to shrink.…