Modern Fraud Attack Lifecycle
Cyber fraud is no longer a single event. It is a multi-stage,…
Optimize your cloud strategy, protect critical data, and ensure compliance with our expert cloud security consulting services.

At COE Security, we deliver Comprehensive Cloud Security Solutions designed to protect your cloud infrastructure, applications, and data from evolving cyber threats. As organizations increasingly migrate to the cloud for scalability and efficiency, securing cloud environments becomes critical to maintaining operational integrity and compliance.
Our cloud security offerings cover major platforms like AWS, Azure, and Google Cloud, ensuring that your cloud configurations, access controls, workloads, and data are secure against misconfigurations, insider threats, and external attacks. We help you implement a shared responsibility model that clearly defines and strengthens your security posture across IaaS, PaaS, and SaaS environments.
With COE Security, you gain visibility, control, and confidence in your cloud deployments whether you’re running a hybrid model or a fully cloud-native infrastructure.
Assess Cloud Security Needs and Objectives: Align cloud security strategies with business goals, compliance requirements, and risk profiles to establish clear objectives.
Evaluate Existing Cloud Architecture and Infrastructure: Review current cloud configurations, services, and vendor agreements to identify potential security gaps.
Define Cloud Security Policies and Governance Frameworks: Establish governance structures, policies, and guidelines for managing cloud resources securely and efficiently.
Implement Identity and Access Management (IAM): Set up robust IAM practices to control user access, enforce MFA, and manage permissions across cloud platforms.
Ensure Data Protection and Privacy Controls: Deploy encryption, tokenization, and secure storage for sensitive data both in transit and at rest within cloud environments.
Secure Cloud Application Deployment: Review DevOps pipelines and ensure secure configuration and deployment practices for cloud-native applications.
Establish Continuous Monitoring and Incident Response: Implement tools and protocols to monitor cloud environments for threats and prepare for rapid response to incidents.
Test Cloud Security Configurations and Compliance: Conduct regular penetration testing, vulnerability scanning, and compliance assessments to ensure cloud security measures are effective.
Optimize Cloud Cost and Security Management: Identify cost-effective security solutions that provide adequate protection without compromising on cloud efficiency or scalability.
Provide a Roadmap for Cloud Security Maturity: Develop a phased plan to continuously improve cloud security practices and capabilities as the organization scales.
Tailored Security Strategy for Your Cloud Environment: We design cloud security plans that match your unique business requirements and cloud architecture.
Holistic Cloud Security Governance: Our consulting ensures strong governance over your cloud resources, addressing both security and compliance needs.
Expertise in Multi-Cloud and Hybrid Environments: We support organizations using single or multi-cloud environments, ensuring security across diverse platforms.
Robust Data Protection and Privacy: We ensure that your cloud data is protected with best-in-class encryption, tokenization, and privacy measures.
Seamless Integration with DevOps: Our approach integrates security into your DevOps pipeline, ensuring secure application deployment in the cloud.
Advanced Threat Monitoring and Incident Response: We implement continuous monitoring systems to detect and respond to threats in real time.
Cost-Effective Security Solutions: We optimize security investments to ensure that cloud security does not compromise your budget or scalability.
Proven Expertise in Cloud Compliance: We help you meet key regulatory requirements like GDPR, HIPAA, and PCI DSS within your cloud environment.
Scalable Cloud Security Practices: Our strategies grow with your organization, adapting to new cloud services and emerging threats.
Experienced Cloud Security Advisors: COE Security offers deep expertise in securing cloud environments across industries, ensuring your cloud adoption is secure and sustainable.
Cloud environments are increasingly becoming targets for cyberattacks, making it essential to identify vulnerabilities before malicious actors can exploit them. Cloud Security/Penetration Testing simulates real-world attacks on your cloud infrastructure to uncover weaknesses in your systems, configurations, and processes. Our expert team performs thorough assessments to test the robustness of your cloud security measures, identifying any gaps in access controls, data protection protocols, and overall security posture. Through detailed vulnerability analysis, we help you mitigate risks and ensure your cloud infrastructure remains secure, scalable, and resilient against evolving threats.

Application Security Consulting focuses on securing the applications that power your cloud environment. In today’s digital landscape, application vulnerabilities are often the entry point for cyberattacks. Our experts work closely with your development teams to implement security best practices throughout the Software Development Life Cycle (SDLC). From threat modeling to secure code reviews, we ensure that security is an integral part of your application development process. Our proactive approach helps you build secure, high-performance applications while minimizing risks associated with data breaches, compliance violations, and reputational damage.

Achieving and maintaining compliance in the cloud can be complex, especially as regulations continue to evolve. Compliance as a Service offers expert guidance and support to help your organization adhere to critical standards such as GDPR, HIPAA, SOC 2, and PCI-DSS, among others. We provide end-to-end compliance solutions that include gap assessments, risk management, and the implementation of controls to meet regulatory requirements. By leveraging our experience, your organization can stay compliant without the need for extensive internal resources. With our ongoing support, you’ll maintain a robust compliance posture, avoiding fines and penalties while ensuring your customers’ trust.

Cyber resilience is about ensuring that your organization can withstand and recover from cyber incidents. In the cloud, it’s crucial to have systems in place that not only prevent attacks but also ensure business continuity in case of a breach. Our Cyber Resilience services focus on creating a resilient cloud infrastructure that anticipates potential threats and has the necessary response mechanisms in place. We help you design disaster recovery plans, implement data backup solutions, and conduct regular testing to ensure that your cloud environment can quickly recover from any disruption. Our goal is to keep your business operational, regardless of cyber events, and help minimize the impact of security incidents.
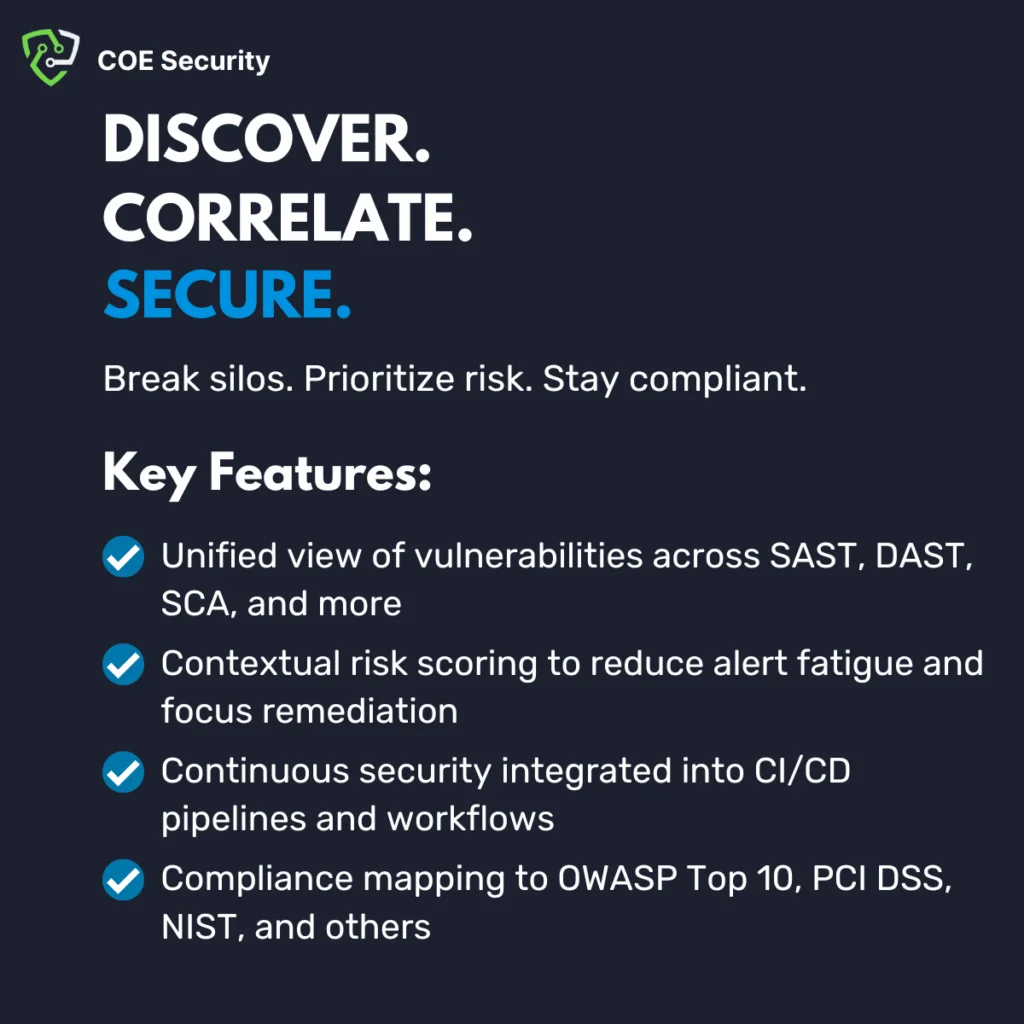
Maintaining a strong security posture in the cloud is an ongoing challenge that requires continuous monitoring, assessment, and improvement. Application Security Posture Management (ASPM) involves the proactive management and monitoring of your applications’ security measures to ensure they align with industry standards and best practices. Our team helps you identify vulnerabilities across your cloud-native applications, prioritize risks based on their potential impact, and take corrective actions to improve security. We integrate automated security testing and monitoring tools to continuously evaluate and enhance the security of your applications, ensuring that they remain resilient and compliant as they evolve.
COE Security empowers your organization with on-demand expertise to uncover vulnerabilities, remediate risks, and strengthen your security posture. Our scalable approach enhances agility, enabling you to address current challenges and adapt to future demands without expanding your workforce.
Your trusted ally in uncovering risks, strengthening defenses, and driving innovation securely.
Certified cybersecurity professionals you can trust.
Testing aligned with OWASP, SANS, and NIST.
Clear reports with practical remediation steps.













the cybersecurity community witnessed a chilling milestone – over 16 billion user…
Global efforts to combat cybercrime continue to gain momentum as law enforcement…