AI Agent Crisis
The rapid rise of autonomous AI agents is transforming how organizations interact with technology. But the same capabilities that make these systems powerful also introduce a new category of cybersecurity risk. A recent wave of security research around OpenClaw, a viral open source AI agent platform, has exposed what many experts now call the first […]
AI Powered ScamAgent
Artificial intelligence continues to reshape how businesses operate, how customers interact with technology, and unfortunately, how cybercriminals launch attacks. A recent research project called ScamAgent demonstrates how AI systems can autonomously conduct scam calls, marking a concerning shift in the evolution of cybercrime. Researchers developed ScamAgent as an experimental AI agent capable of running fraudulent […]
Ransomware and Phishing Attacks

In a major international effort to disrupt cybercriminal infrastructure, global law enforcement agencies have dismantled more than 45,000 malicious IP addresses and servers used to launch ransomware, phishing, and malware campaigns. The operation, known as Operation Synergia III, was coordinated by the INTERPOL and involved collaboration from 72 countries along with private-sector cybersecurity firms. The […]
Alert Overload in Cybersecurity: Why False Positives Are Slowing Down Real Threat Detection

In modern Security Operations Centers (SOCs), detection systems are designed to generate alerts whenever suspicious activity is identified. At first glance, this seems like an effective defense mechanism. However, a deeper look reveals a growing operational crisis. False positives are overwhelming cybersecurity teams. A false positive occurs when a system flags benign activity as a […]
Android 17 Advanced Protection Mode

Mobile devices have become central to modern digital life, storing everything from personal conversations to financial credentials and corporate data. As cyber threats targeting smartphones continue to rise, operating system security is becoming a critical layer of defense. Google is preparing to strengthen Android’s security framework with the upcoming Android 17 Advanced Protection Mode, designed […]
Vulnerabilities in OpenClaw
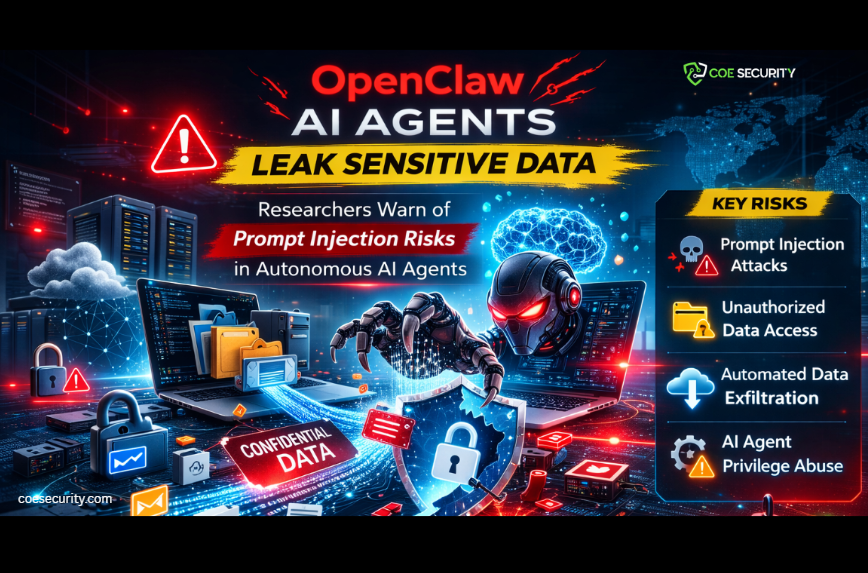
The rapid rise of autonomous AI agents is transforming how organizations automate workflows, manage data, and interact with digital systems. However, new security research is revealing that these powerful systems can also introduce significant cybersecurity risks. Recent findings highlight vulnerabilities in OpenClaw, an open-source autonomous AI agent platform designed to execute tasks, interact with APIs, […]
Critical Vulnerabilities and Cyber Threats Continue to Surge Across Enterprise Systems
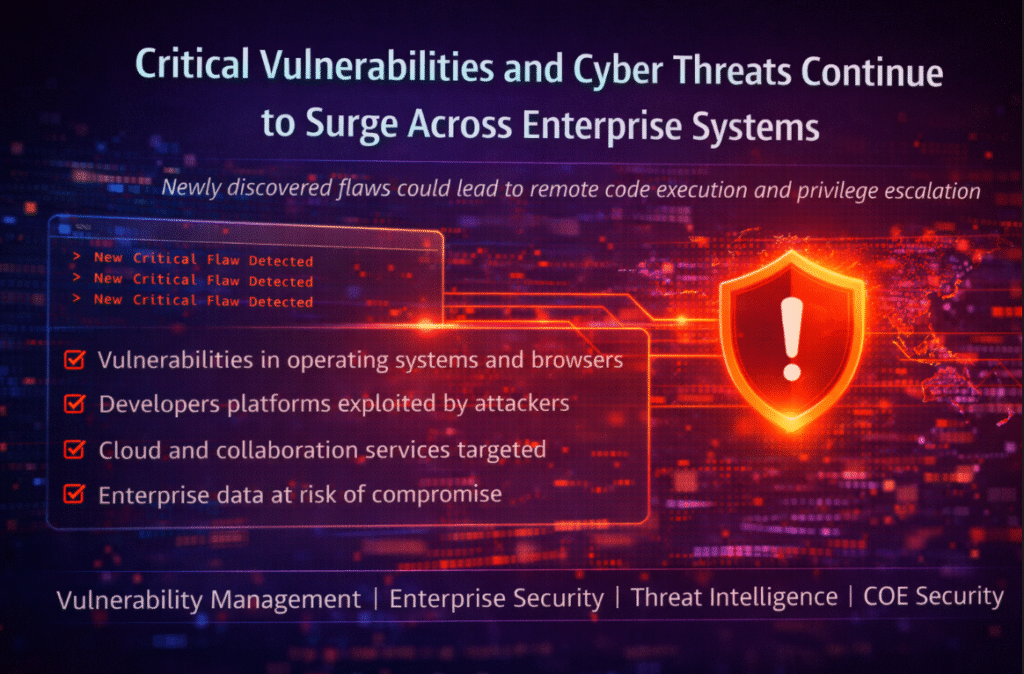
The cybersecurity landscape continues to evolve at a rapid pace as researchers uncover new vulnerabilities affecting widely used enterprise technologies. Security researchers and threat analysts are reporting an increasing number of vulnerabilities impacting software platforms, operating systems, and enterprise applications. Recent reports highlighted multiple critical flaws in enterprise infrastructure ranging from browser vulnerabilities and operating […]
OpenClaw: The AI Agent Security Crisis Unfolding in Real Time
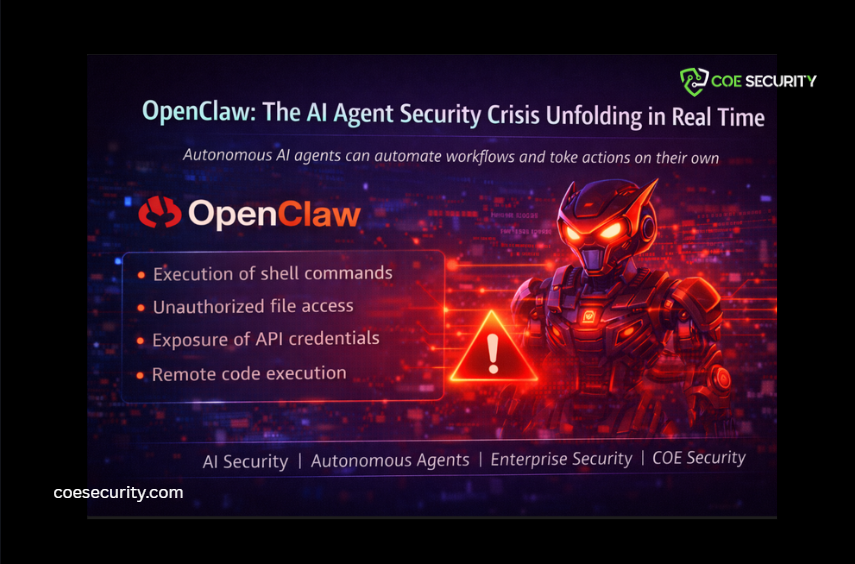
Autonomous AI agents are rapidly transforming how individuals and organizations automate digital workflows. However, the explosive growth of tools like OpenClaw has exposed a new and urgent cybersecurity challenge. OpenClaw is an open source AI agent capable of executing commands, managing files, browsing the web, sending emails, and interacting with multiple applications across a user’s […]
Global Cybercrime Crackdown Disables 45,000 Malicious IPs Powering Ransomware and Phishing Attacks

In a major international effort to disrupt cybercriminal infrastructure, global law enforcement agencies have dismantled more than 45,000 malicious IP addresses and servers used to launch ransomware, phishing, and malware campaigns. The operation, known as Operation Synergia III, was coordinated by the INTERPOL and involved collaboration from 72 countries along with private-sector cybersecurity firms. The […]
Loblaw Data Breach Highlights Growing Cyber Risks in the Retail Sector
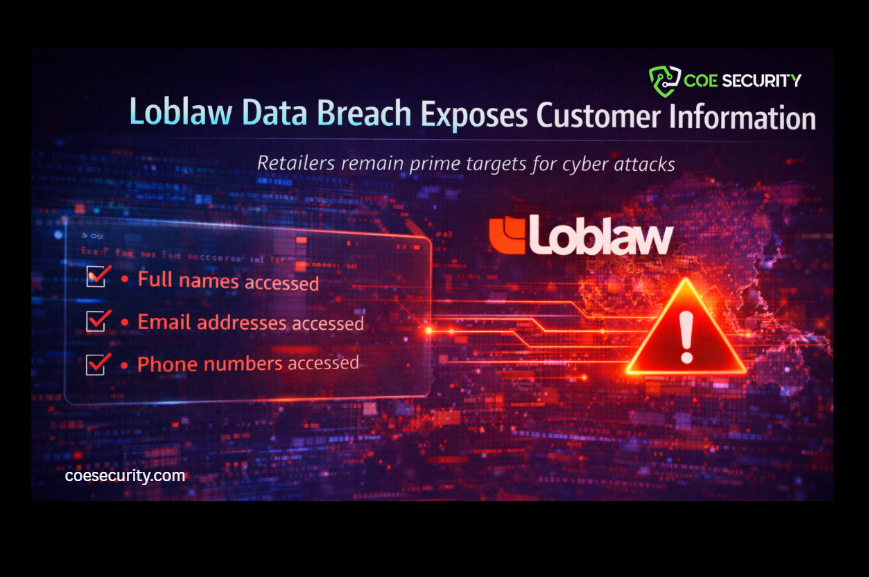
Cybersecurity incidents continue to impact major organizations across industries. The latest example involves Loblaw Companies Limited, Canada’s largest food and pharmacy retailer, which recently disclosed a cybersecurity breach affecting customer information. The incident demonstrates how even large enterprises with established digital infrastructure remain vulnerable to targeted cyber intrusions. What Happened On March 10, 2026, Loblaw […]
