QuirkyLoader: The New Malware Loader
Cybersecurity professionals have uncovered a novel threat named QuirkyLoader-a sophisticated multi-stage malware loader deployed via spam emails that has been active since November 2024. Key Threat Mechanics Spam emails carry an archive containing three elements: a legitimate executable, an encrypted payload disguised as a DLL, and a malicious DLL loader. The benign executable triggers the […]
New Risks for Industrial Control Systems
On August 19, 2025, the Cybersecurity and Infrastructure Security Agency (CISA) issued four urgent advisories targeting vulnerabilities in Industrial Control Systems (ICS). These alerts reveal high-risk flaws in products from Siemens, Tigo Energy, and EG4 Electronics-underscoring the need for faster, smarter defense in critical infrastructure sectors such as energy and manufacturing. Highlights from the Advisories […]
Scattered Spider Hacker Sentenced

The cybercrime landscape witnessed a landmark ruling as a key member of the Scattered Spider hacking group was sentenced to 10 years in prison. This collective has been behind some of the most sophisticated social engineering, phishing, and ransomware campaigns, targeting major industries and exploiting human vulnerabilities as much as technological ones. The sentencing is […]
Clickjacking Threatens Password Managers

Password managers have become the cornerstone of digital security, entrusted with safeguarding sensitive credentials across personal and enterprise environments. However, recent security research has revealed a concerning weakness: clickjacking attacks can exploit the very platforms designed to protect us. Understanding the Threat Clickjacking occurs when a malicious actor overlays hidden frames or deceptive UI elements […]
RingReaper: Linux Malware Outsmarts EDR

A new strain of malware targeting Linux environments is pushing the boundaries of stealth and evasion. Known as RingReaper, this post-compromise agent exploits a modern Linux kernel capability-io_uring-to bypass the monitoring mechanisms that traditional endpoint detection and response (EDR) systems rely on. Io_uring, introduced in Linux kernel 5.1, facilitates efficient asynchronous I/O by batching operations […]
AI-Powered Phishing Scams Unveiled

Cybercriminals are turning generative AI platforms into weapons, using them to spin up convincing phishing websites in moments. Attackers prompt AI-based site builders with simple company descriptions and receive polished, ready-to-publish phishing pages-complete with realistic branding and service narratives-capable of outmaneuvering standard detection systems. These fake sites often lead to credential-stealing traps, duping unsuspecting users […]
Google Rewards $250K for Chrome Exploit
Google awarded a groundbreaking $250,000 bounty to security researcher Micky for identifying a critical remote code execution flaw in Chrome. The vulnerability enabled malicious websites to bypass Chrome’s sandbox protection-escalating risks across user systems. About the Vulnerability The issue stemmed from a flaw in Chrome’s Inter-Process Communication system, specifically within the IPCZ transport layer. A […]
Gmail Phishing: Rising Threat

Phishing remains one of the most dangerous and effective cyber threats, and Gmail users are increasingly becoming prime targets. Recently, cybersecurity researchers have uncovered a sophisticated Gmail phishing campaign designed to steal login credentials and compromise user trust. These attacks rely on deceptive emails crafted to appear authentic, often leveraging urgent prompts to trick users […]
APT Hits Taiwan’s Web Core
A sophisticated threat group known as UAT-7237 has been linked to a large-scale cyber campaign breaching Taiwanese government and educational web servers. This Chinese-speaking APT, believed to be a subgroup of UAT-5918, has been active since at least 2022 and is now using heavily modified open-source hacking tools to carry out highly targeted attacks. Attack […]
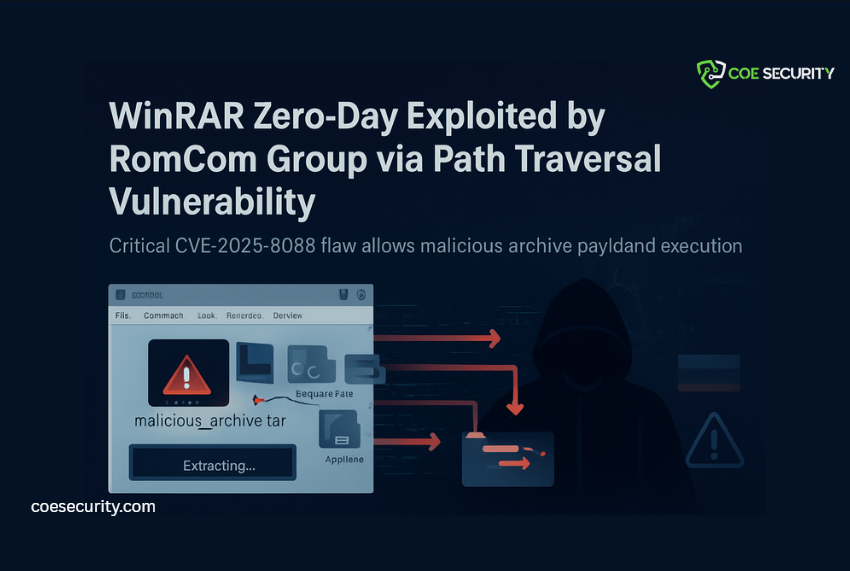
WinRAR Zero-Day Hit by RomCom
A critical security flaw in WinRAR, tracked as CVE-2025-8088, is under active exploitation by the Russia-linked hacking group RomCom. The vulnerability allows malicious .rar archives to extract files into unintended system paths-such as the Startup folder-leading to automatic malware execution upon reboot. Because WinRAR does not have an auto-update function, this flaw remains a significant […]
