New Era of Blockchain-Backed Cyber Threats

Cyber attackers continue to evolve their techniques, combining phishing, automation, and decentralized technologies to make detection significantly harder. A recently identified threat known as the OCRFix botnet demonstrates how modern malware campaigns are shifting toward stealthier and more resilient command infrastructures by leveraging blockchain technologies alongside advanced social engineering tactics. Understanding the OCRFix Threat Landscape […]
Ethical Hacking Tools in 2026
In today’s dynamic threat landscape, ethical hacking is no longer a niche discipline-it has become a cornerstone of modern cybersecurity strategy. As organizations grapple with increasingly sophisticated threats, the role of ethical hackers-professionals authorized to find and responsibly disclose vulnerabilities-has never been more critical. Ethical hacking tools empower these practitioners to simulate real-world attacks, test […]
Critical Data Governance
A massive cryptocurrency theft has rocked digital finance and government technology stakeholders after an exposed wallet seed phrase led to the disappearance of $48 million worth of crypto assets. The incident, linked to a South Korean tax agency’s unsecured storage of wallet seed data, underscores a growing blind spot in how sensitive cryptographic information is […]
$82,000 in charges in 48 hours
A new security finding has uncovered a significant cloud and API security vulnerability affecting users of Google Cloud Platform related to the rollout of Gemini AI services. Security researchers have discovered that nearly 3,000 Google Cloud API keys that were previously considered non-sensitive billing tokens are now exposed on the public internet and can be […]
Telecom & Customer Data Risks

A major data breach has hit Odido, exposing personal information of millions of customers and underscoring ongoing risks in telecom data security. According to public reports, a threat actor gained unauthorized access to Odido’s systems and leaked sensitive subscriber data on underground forums. Compromised information reportedly included customer names, contact details, subscription records, and in […]
Cloud Security Concerns

A significant data exposure incident linked to Abu Dhabi Finance Week 2026 has brought cloud security governance back into sharp focus across the global financial ecosystem. Sensitive records belonging to more than 700 high-profile attendees, including global executives, policymakers, and financial leaders, were reportedly exposed due to a misconfigured cloud storage environment. The exposed data […]
AUAE Foils Major AI-Driven Cyberattack Targeting Government Systems
In a significant cybersecurity development in 2026, the United Arab Emirates successfully prevented a large-scale, AI-driven cyberattack targeting critical government digital infrastructure. Authorities reported that the attack was highly coordinated and leveraged advanced artificial intelligence techniques to attempt infiltration of sensitive national systems. Swift detection and response mechanisms neutralized the threat before operational damage could […]
Resilient Data Security Architecture in 2026
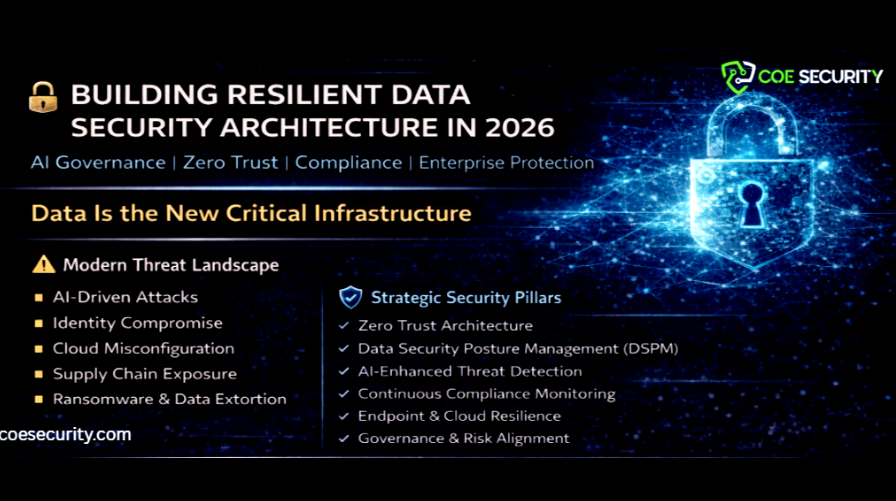
In 2026, data security has evolved into a strategic enterprise mandate. Organizations operate across hybrid cloud environments, SaaS platforms, AI systems, remote work infrastructures, and interconnected supply chains. As digital transformation accelerates, the attack surface expands exponentially. Cyber adversaries are leveraging automation, artificial intelligence, identity exploitation, and infrastructure manipulation to compromise sensitive data at scale. […]
Essential e-Signature Solutions for Cybersecurity
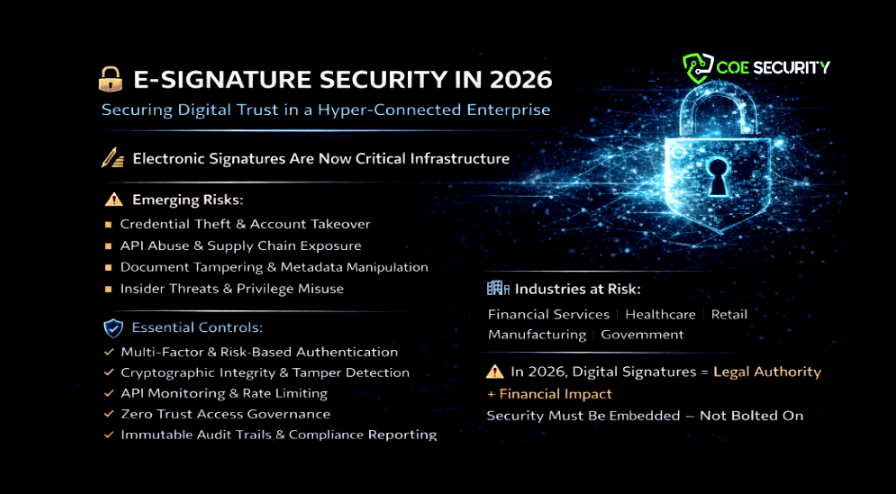
As digital transformation accelerates, electronic signatures have become a core part of business operations – from contracts and procurement approvals to client onboarding and legal attestations. With this growing adoption, cybersecurity considerations around e-signature platforms have moved to the top of both risk management and regulatory compliance agendas. (cybersecuritynews.com) In 2026, the convergence of remote […]
Google Suspends OpenClaw Accounts Amid Malware Abuse – What Security Teams Must Know

In a proactive security move, Google has suspended a number of OpenClaw accounts after discovering widespread abuse of the threat hunting platform by malicious actors. The takedown underscores how legitimate cybersecurity tools can be co-opted for offensive operations when governance and oversight are lacking. OpenClaw – widely used by defenders for threat hunting, investigation, and […]
