A Silent Entry Point to Enterprise Compromise
A newly disclosed critical vulnerability in Fortinet’s FortiClient Endpoint Management Server (EMS) is a stark reminder that attackers do not always rely on complex exploits. Sometimes, a single exposed interface is enough to compromise an entire environment. The vulnerability, tracked as CVE-2026-21643, affects FortiClient EMS version 7.4.4 and carries a critical severity score of over […]
Fortinet FortiClient EMS Zero-Day: A Silent Entry Point to Enterprise Compromise
A newly disclosed critical vulnerability in Fortinet’s FortiClient Endpoint Management Server (EMS) is a stark reminder that attackers do not always rely on complex exploits. Sometimes, a single exposed interface is enough to compromise an entire environment. The vulnerability, tracked as CVE-2026-21643, affects FortiClient EMS version 7.4.4 and carries a critical severity score of over […]
The Real Beginning of Cyber Fraud: Why Prevention Must Start Before Login
Cybersecurity conversations often focus on breaches, stolen credentials, and account takeovers. But the reality is far more subtle and far more dangerous. Fraud rarely begins at the moment of compromise. It starts much earlier, often unnoticed, within the very systems designed to welcome users. Modern attackers do not break in. They blend in. The earliest […]
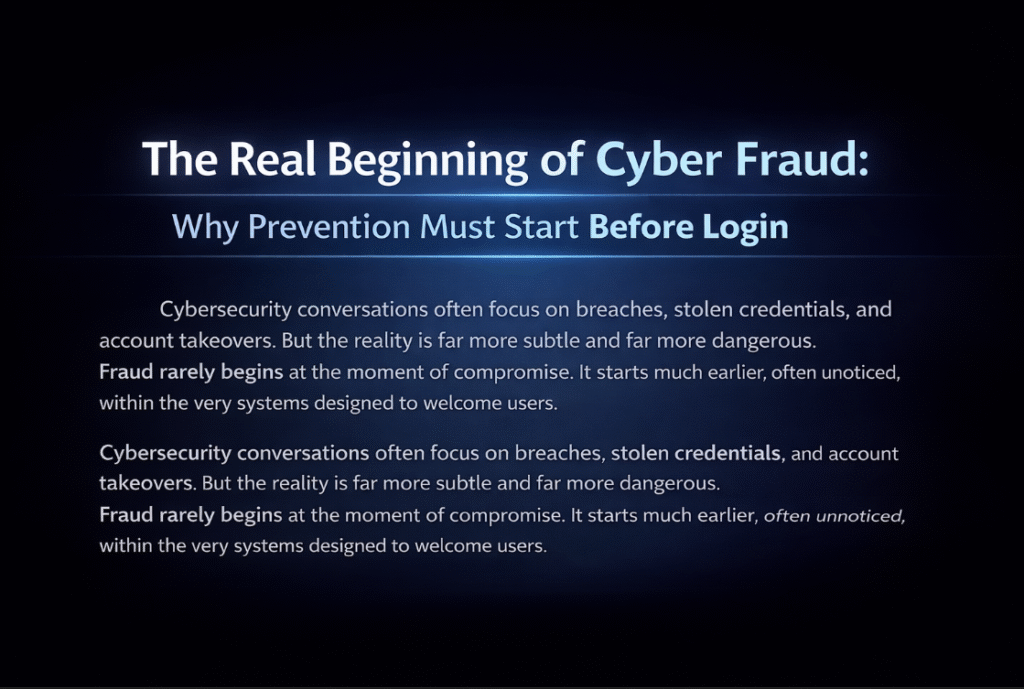
Modern Fraud Attacks Are Evolving Fast: From Bot Signups to Account Takeovers
How Modern Fraud Works Today’s fraud attacks typically follow a structured path: Stage 1: Bot Signups Attackers create thousands of fake accounts using automation tools. Stage 2: Account Validation They test which accounts are active, valid, and usable. Stage 3: Credential Stuffing Leverage stolen credentials to gain access to real user accounts. Stage 4: Account […]
The Growing Link Between Cybersecurity and National Security

A recent regulatory move to restrict the use of certain foreign-made routers has sparked global discussion. At first glance, it may seem like a political decision. But in reality, it reflects a deeper concern: Network infrastructure is now a national security asset. Why Routers Matter More Than Ever Routers are not just connectivity devices. They […]
Outages Are More Than Just Technical Issues

A recent disruption affecting a major social media platform caused widespread issues with posting and messaging. For most users, it was just an inconvenience. But from a cybersecurity perspective, it highlights something much deeper: Downtime is not just an availability issue. It can become a security risk. What Happens During an Outage When platforms experience […]
Third-Party Risk Is Out of Control

A recent data breach impacting a major retail organization has once again highlighted a critical weakness in modern cybersecurity: Your biggest risk may not be your own systems. It may be your third-party vendors. What Happened The breach involved unauthorized access to sensitive data linked to customer and operational systems. While investigations are ongoing, early […]
False Positives Are the Real Threat
Cybersecurity teams are not failing because of a lack of tools. They are failing because of too many alerts. Modern security operations centers (SOCs) are overwhelmed with thousands of alerts every day. The majority of them are false positives. And that is where the real danger lies. The Hidden Problem Security systems are designed to […]
Secure mobile devices and enterprise access points

Google’s latest move to introduce Advanced Protection Mode in Android signals a major shift in mobile security. As cyber threats continue to evolve, smartphones are no longer just personal devices. They are gateways to sensitive data, financial systems, and enterprise access. What Is Advanced Protection Mode Advanced Protection Mode is designed to provide enhanced security […]
Why IP Takedowns Are Not a Complete Solution
Authorities recently carried out a large-scale operation, taking down tens of thousands of malicious IP addresses linked to cybercrime activity. At first glance, this sounds like a major win for cybersecurity. But here is the reality: Taking down IPs does not stop attackers. It only slows them down. Why IP Takedowns Are Not a Complete […]
