WinRAR Zero-Day Hit
A critical security flaw in WinRAR, tracked as CVE-2025-8088, is under active exploitation by the Russia-linked hacking group RomCom. The vulnerability allows malicious .rar archives to extract files into unintended system paths-such as the Startup folder-leading to automatic malware execution upon reboot. Because WinRAR does not have an auto-update function, this flaw remains a significant […]
AWSDoor illustrates a broader shift in attacker tactics

A newly identified malware technique known as AWSDoor has raised serious concerns across the cybersecurity community. This method enables attackers to maintain persistence within AWS cloud environments by masking malicious activities as legitimate processes. With organizations increasingly dependent on AWS, the ability for adversaries to hide in plain sight significantly increases risk exposure. Why This […]
$82,000 in charges
A new security finding has uncovered a significant cloud and API security vulnerability affecting users of Google Cloud Platform related to the rollout of Gemini AI services. Security researchers have discovered that nearly 3,000 Google Cloud API keys that were previously considered non-sensitive billing tokens are now exposed on the public internet and can be […]
Palo Alto Cortex XDR BIOC Rules
Endpoint detection and response platforms are designed to identify and stop advanced threats. However, recent research has revealed that even defensive mechanisms themselves can become targets. A study focusing on Palo Alto Cortex XDR highlights how encrypted Behavioral Indicators of Compromise, known as BIOC rules, can be decrypted and potentially exploited. This finding sheds light […]
The AI Agent Security Crisis Unfolding in Real Time
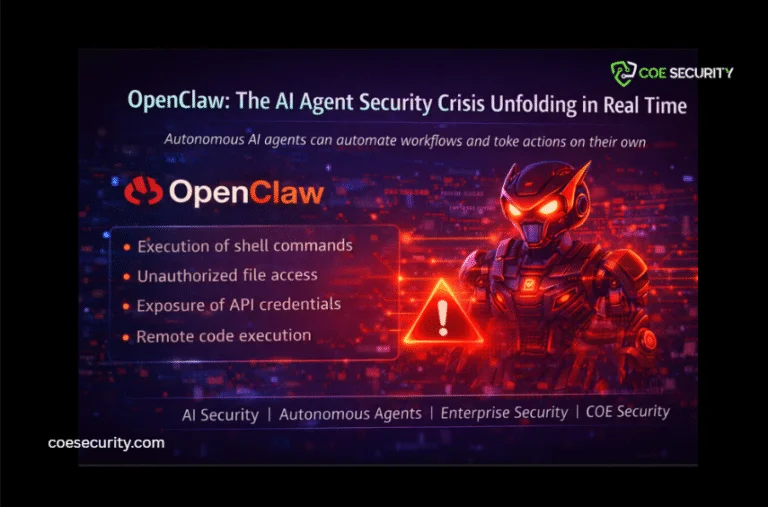
Autonomous AI agents are rapidly transforming how individuals and organizations automate digital workflows. However, the explosive growth of tools like OpenClaw has exposed a new and urgent cybersecurity challenge. OpenClaw is an open source AI agent capable of executing commands, managing files, browsing the web, sending emails, and interacting with multiple applications across a user’s […]
Banks Under Siege

Cybersecurity threats are no longer limited to sophisticated malware built in the shadows. Increasingly, open-source tools-widely used for legitimate testing and development-are being exploited by cybercriminals to breach financial institutions across Africa. This evolution marks a significant shift in attacker behavior. Open-source frameworks such as Metasploit, Cobalt Strike, and Empire are enabling attackers to conduct […]
npm Packages Disguised as Solara Executor Target Discord, Browsers, and Crypto Wallets
Open source ecosystems play a vital role in modern software development. Platforms such as npm allow developers to quickly integrate libraries and tools into their applications. However, this convenience also creates opportunities for threat actors to distribute malicious code through seemingly legitimate packages. Security researchers recently identified a campaign involving malicious npm packages posing as […]
Botnet Infrastructure Exposed Through Open Directory Leak

Cyber threat intelligence continues to uncover how attackers build and operate covert infrastructure to carry out large scale campaigns. In a recent discovery, researchers exposed a botnet linked to Iran after an unsecured open directory revealed details of a 15 node relay network. This incident highlights a recurring reality in cybersecurity. Even well structured malicious […]
Critical Risks in CI/CD Supply Chains

A recent cybersecurity incident involving Trivy, one of the most widely used open-source vulnerability scanners, has raised serious concerns about the security of modern software supply chains. Researchers uncovered that attackers exploited weaknesses in Trivy’s ecosystem to inject malicious scripts into trusted workflows, potentially compromising CI/CD pipelines and exposing sensitive credentials. What Happened The incident […]
7,500 Magento Websites Compromised

A large-scale cyber campaign has recently exposed the vulnerabilities of modern e-commerce infrastructure, with attackers compromising approximately 7,500 Magento-based websites across multiple industries and regions. The attack, identified as a widespread defacement campaign, impacted nearly 15,000 hostnames globally, affecting e-commerce platforms, enterprise systems, and even government-related domains. What Happened Security researchers observed attackers gaining unauthorized […]
