Ancillary Systems Are High-Value Targets
On December 15, 2025, SoundCloud confirmed unauthorized access to user data affecting approximately 20% of its global user base. The attackers exfiltrated email addresses and public profile information. Importantly, no passwords, authentication secrets, or financial data were compromised. From a narrow technical perspective, this distinction matters. It prevented immediate account takeover, direct financial fraud, and […]
chained exploitation technique
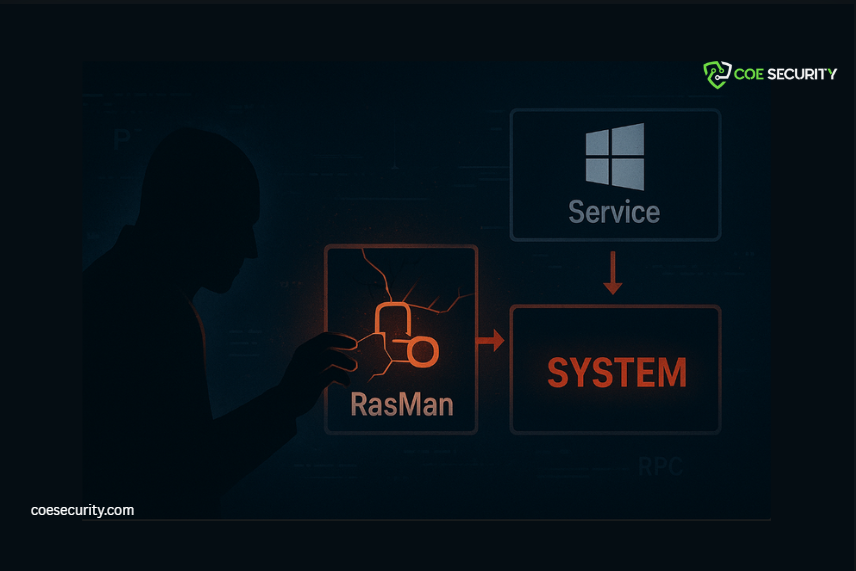
A critical weakness has been identified in Windows Remote Access Connection Manager (RasMan) that enables local attackers to achieve SYSTEM-level code execution. What makes this issue especially dangerous is not a single vulnerability-but a chained exploitation technique that breaks long-standing Windows security assumptions. Executive Summary Impact: Full local privilege escalation to NT AUTHORITY\SYSTEM Attack Type: […]
Critical limitation of email authentication standards
Email security frameworks have matured significantly over the past decade. SPF, DKIM, and DMARC are now widely deployed and effective at stopping impersonation and spoofing from external attackers. Yet recent activity attributed to the BlindEagle threat group highlights a growing weakness that technical controls alone cannot address: misplaced trust in internal systems. This campaign demonstrates […]
Malicious Chrome Extensions

A coordinated campaign of malicious Chrome extensions is actively targeting enterprise SaaS platforms-specifically HR and ERP systems such as Workday, NetSuite, and SAP SuccessFactors. This is not opportunistic malware. It is a deliberate identity takeover operation engineered to bypass modern security controls by exploiting the most trusted layer in the enterprise stack: the browser. With […]
Microsoft 365 credentials

A new phishing campaign is exploiting trusted cloud infrastructure-and it changes the threat model entirely. Attackers are abusing Google Cloud services to bypass traditional email security controls and steal Microsoft 365 credentials. Any organisation running Microsoft 365 is a potential target. This is not classic phishing. This is trusted cloud abuse. Phishing attacks no longer […]
vulnerability (CVE-2025-69258)

A critical vulnerability (CVE-2025-69258) has been disclosed in Trend Micro Apex Central for Windows, exposing on-premise deployments to remote code execution with SYSTEM privileges. This is not theoretical-this impacts the core security infrastructure of organisations. The Issue Tracked as CVE-2025-69258, CVSS 9.8 Root cause: unsafe DLL loading (LoadLibraryEX) Vulnerable process: MsgReceiver.exe Attack vector: crafted message […]
Stolen Data Against the Thief

Why Data Resilience Is the Next Frontier of AI Security For years, AI security focused on models: prompt injection, jailbreaks, poisoning during training, and inference-time manipulation. But a more dangerous shift is underway. AI systems are no longer being attacked through their code. They are being attacked through their data. Recent research demonstrates a new […]
Microsoft 365 credentials

A new phishing campaign is exploiting trusted cloud infrastructure-and it changes the threat model entirely. Attackers are abusing Google Cloud services to bypass traditional email security controls and steal Microsoft 365 credentials. Any organisation running Microsoft 365 is a potential target. This is not classic phishing. This is trusted cloud abuse. Phishing attacks no longer […]
Phishing Campaign Abuses Google Infrastructure

This is not spoofing. This is platform abuse. A newly identified phishing campaign marks a dangerous shift in how attackers exploit trust on the internet. Instead of impersonating Google through fake domains or lookalike emails, threat actors are now abusing legitimate Google infrastructure itself to conduct large-scale credential theft. Thousands of organizations worldwide have already […]
Shai Hulud Variant

A known malware strain has resurfaced-with purpose, planning, and continued investment. Security researchers have identified a new, heavily modified variant of the Shai Hulud malware, and this is not a recycled threat or a low-effort fork. The changes observed indicate active maintenance, deliberate obfuscation, and functional refinement by the original threat actors. Most critically, development […]
